Yesterday, we wrote a little bit about the new speculative execution vulnerability known as L1 Terminal Fault (L1TF) or Foreshadow, and a reader – MHSadri – pointed to an interesting script that checks for all three speculative execution vulnerabilities, and runs in Linux and BSD (FreeBSD, NetBSD, DragonFlyBSD) across multiple architectures: Intel x32, AMD64, Arm and ARM64. Other architectures will also work, but mitigation reporting may not be correct.
So I tried it on my own machine, a computer running Ubuntu 18.04 on an AMD FX8350 processor.
|
1 2 |
git clone https://github.com/speed47/spectre-meltdown-checker/ cd spectre-meltdown-checker |
The developer recommends to check the script manually first, just for security sake. You can have two way to run it: either directly inside your OS, or via docker which may be a better idea since it would not be able to mess with your system especially I had to run it with sudo to avoid permission issues.
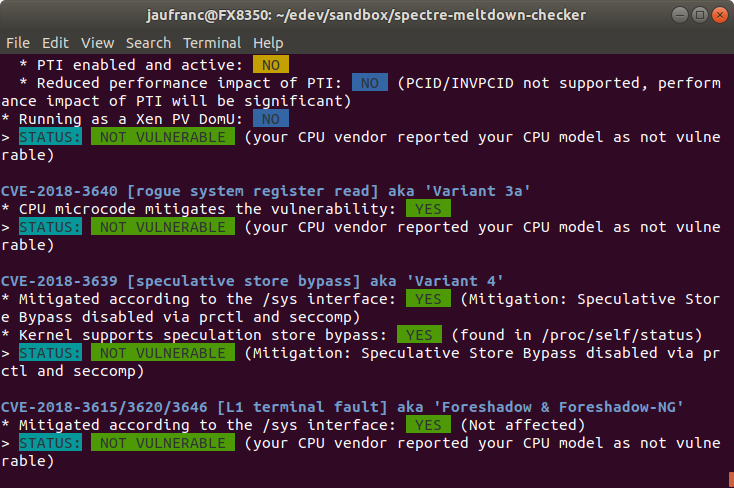
Here’s the full output while running the script in a terminal window in my computer:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 |
sudo ./spectre-meltdown-checker.sh Spectre and Meltdown mitigation detection tool v0.39-6-gdd67fd9 Checking for vulnerabilities on current system Kernel is Linux 4.15.0-32-generic #35-Ubuntu SMP Fri Aug 10 17:58:07 UTC 2018 x86_64 CPU is AMD FX(tm)-8350 Eight-Core Processor Hardware check * Hardware support (CPU microcode) for mitigation techniques * Indirect Branch Restricted Speculation (IBRS) * SPEC_CTRL MSR is available: NO * CPU indicates IBRS capability: NO * CPU indicates preferring IBRS always-on: NO * CPU indicates preferring IBRS over retpoline: NO * Indirect Branch Prediction Barrier (IBPB) * PRED_CMD MSR is available: YES * CPU indicates IBPB capability: YES (IBPB_SUPPORT feature bit) * Single Thread Indirect Branch Predictors (STIBP) * SPEC_CTRL MSR is available: NO * CPU indicates STIBP capability: NO * CPU indicates preferring STIBP always-on: NO * Speculative Store Bypass Disable (SSBD) * CPU indicates SSBD capability: YES (AMD non-architectural MSR) * L1 data cache invalidation * FLUSH_CMD MSR is available: NO * CPU explicitly indicates not being vulnerable to Variant 4 (SSB_NO): NO * Hypervisor indicates host CPU might be vulnerable to RSB underflow (RSBA): NO * CPU microcode is known to cause stability problems: NO (model 0x2 family 0x15 stepping 0x0 ucode 0x6000852 cpuid 0x600f20) * CPU microcode is the latest known available version: UNKNOWN (latest microcode version of your CPU is not known to this script) * CPU vulnerability to the speculative execution attack variants * Vulnerable to Variant 1: YES * Vulnerable to Variant 2: YES * Vulnerable to Variant 3: NO * Vulnerable to Variant 3a: NO * Vulnerable to Variant 4: YES * Vulnerable to Variant l1tf: NO CVE-2017-5753 [bounds check bypass] aka 'Spectre Variant 1' * Mitigated according to the /sys interface: YES (Mitigation: __user pointer sanitization) * Kernel has array_index_mask_nospec: YES (1 occurrence(s) found of x86 64 bits array_index_mask_nospec()) * Kernel has the Red Hat/Ubuntu patch: NO * Kernel has mask_nospec64 (arm64): NO > STATUS: NOT VULNERABLE (Mitigation: __user pointer sanitization) CVE-2017-5715 [branch target injection] aka 'Spectre Variant 2' * Mitigated according to the /sys interface: YES (Mitigation: Full AMD retpoline, IBPB) * Mitigation 1 * Kernel is compiled with IBRS support: YES * IBRS enabled and active: NO * Kernel is compiled with IBPB support: YES * IBPB enabled and active: YES * Mitigation 2 * Kernel has branch predictor hardening (arm): NO * Kernel compiled with retpoline option: YES * Kernel compiled with a retpoline-aware compiler: YES (kernel reports full retpoline compilation) > STATUS: NOT VULNERABLE (Full retpoline + IBPB are mitigating the vulnerability) CVE-2017-5754 [rogue data cache load] aka 'Meltdown' aka 'Variant 3' * Mitigated according to the /sys interface: YES (Not affected) * Kernel supports Page Table Isolation (PTI): YES * PTI enabled and active: NO * Reduced performance impact of PTI: NO (PCID/INVPCID not supported, performance impact of PTI will be significant) * Running as a Xen PV DomU: NO > STATUS: NOT VULNERABLE (your CPU vendor reported your CPU model as not vulnerable) CVE-2018-3640 [rogue system register read] aka 'Variant 3a' * CPU microcode mitigates the vulnerability: YES > STATUS: NOT VULNERABLE (your CPU vendor reported your CPU model as not vulnerable) CVE-2018-3639 [speculative store bypass] aka 'Variant 4' * Mitigated according to the /sys interface: YES (Mitigation: Speculative Store Bypass disabled via prctl and seccomp) * Kernel supports speculation store bypass: YES (found in /proc/self/status) > STATUS: NOT VULNERABLE (Mitigation: Speculative Store Bypass disabled via prctl and seccomp) CVE-2018-3615/3620/3646 [L1 terminal fault] aka 'Foreshadow & Foreshadow-NG' * Mitigated according to the /sys interface: YES (Not affected) > STATUS: NOT VULNERABLE (your CPU vendor reported your CPU model as not vulnerable) Need more detailed information about mitigation options? Use --explain A false sense of security is worse than no security at all, see --disclaimer |
So if I read that right my machine implements mitigation for all variant of Spectre and Meltdown, and is not affected by L1 terminal fault as expected for an AMD processor.
However, trying on some remote computer with an Intel Xeon processor tells a different story:
|
1 2 3 4 5 6 7 8 9 10 |
CVE-2018-3640 [rogue system register read] aka 'Variant 3a' * CPU microcode mitigates the vulnerability: NO > STATUS: VULNERABLE (an up-to-date CPU microcode is needed to mitigate this vulnerability) CVE-2018-3639 [speculative store bypass] aka 'Variant 4' * Kernel supports speculation store bypass: NO > STATUS: VULNERABLE (Neither your CPU nor your kernel support SSBD) CVE-2018-3615/3620/3646 [L1 terminal fault] aka 'Foreshadow & Foreshadow-NG' > STATUS: VULNERABLE (your CPU is known to be vulnerable, and your kernel doesn't report that it mitigates the issue, but more thorough mitigation checking by this script is being worked on (check often for new versions!)) |
The system is not only vulnerable to L1 terminal fault, but also to Meltdown variant 3a and 4. Other variants of Spectre and Meltdown (not shown) are “NOT VULNERABLE” with mitigations already implemented.

Jean-Luc started CNX Software in 2010 as a part-time endeavor, before quitting his job as a software engineering manager, and starting to write daily news, and reviews full time later in 2011.
Support CNX Software! Donate via cryptocurrencies, become a Patron on Patreon, or purchase goods on Amazon or Aliexpress




in my system laravel not to instal any one to help me
A nifty script, with one remark: on arm big.LITTLE it reports the CPU as the first encountered uarch, even though the checks are performed against all present uarchs — so for instance a machine with big A72 cores is properly identified as vulnerable to Spectre variants 1, 2, 3a & 4, even though the CPU might be reported as A53.
I hate running unknown tools under sudo and preferred to read it first. That’s a very well written script, like I’ve not seen for a long time. And in addition it’s useful, maybe it will remind many admins that it’s still possible to write useful tools without having to install $whatever_new_language_of_the_day. As is often the case, well written scripts work well 🙂 Just an advice to the author, instead of requiring sudo for the whole script, it’s often better to have a SUDO variable in it for the rare commands that require sudo, and ask users to run “SUDO=sudo ./script”.… Read more »
@cnx-software, using AMD CPU? Other people are not so lucky! See some pretty shocking stats about the effectiveness of those flaws in clouds, VPSes laptops, desktops, … as well as softwares (Web Browsers, OS, Antivirus, …) Summary of the patch status for Meltdown / Spectre https://github.com/hannob/meltdownspectre-patches Meltdown and Spectre .. for normal people: https://github.com/neuhalje/presentation_meltdown_spectre https://meltdownattack.com/meltdown.pdf So, according to the results, if you are browsing the web, you may be targeting by hackers’ espionage through browser’s other tab! Multi-tab browsers became the new toy in the hands of hackers / intelligence agencies to get what they are looking for! I have… Read more »
Check out “bug” in /proc/cpuinfo:
My brandnew i3 (with Linux 4.1something)
$ grep bug /proc/cpuinfo | sort -u
bugs : cpu_meltdown spectre_v1 spectre_v2 spec_store_bypass
An old XEON (with Linux 3.something)
$ grep bug /proc/cpuinfo | sort -u
fdiv_bug : no
f00f_bug : no
coma_bug : no
An old Atom (with Linux 3.something)
$ grep bug /proc/cpuinfo | sort -u
coma_bug : no
f00f_bug : no
fdiv_bug : no