OpenSSL 3.0 has just been released after three years of development, and over 7,500 commits and contributions from over 350 different authors with a new FIPS module that awaits FIPS 140-2 validation by the end of the year, improved documentation, and a change to an Apache License 2.0.
OpenSSL’s reputation took a serious hit in 2014 with the Hearbleed bug that allowed attackers to steal the information protected by the SSL/TLS encryption used for most secure Internet communication. The bug was introduced in 2012, and it took almost two years to be fixed. Yet, despite the fix, many projects switched to other SSL libraries like LibreSSL, WolfSSL, or mbedTLS.
But it’s good the project is still very much active, and OpenSSL 3.0 succeeds OpenSSL 1.1.1 released in September 2018. Who knows what OpenSSL 2.0…
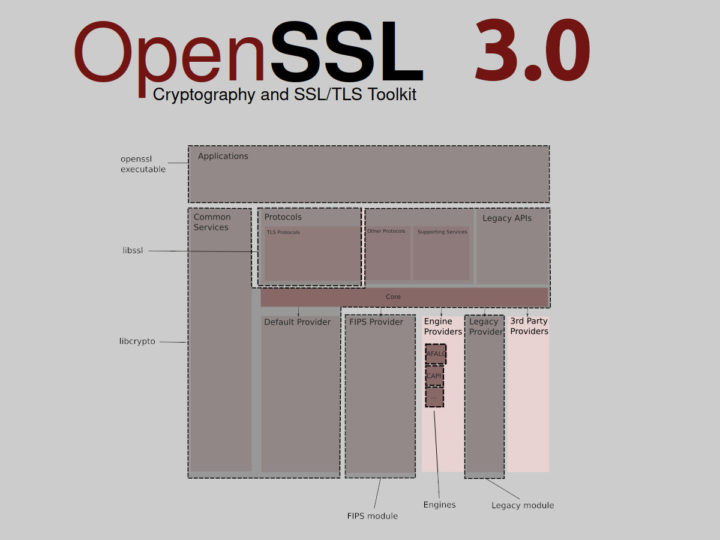
One of the main changes is support for the Provider concept, and OpenSSL 3.0 comes with 5 different providers as standard:
- Default Provider – Implements a set of default algorithms.
- FIPS Provider – Implements a set of algorithms that are FIPS validated and includes the following supporting services:
- POST: Power On Self Test
- KAT: Known Answer Tests
- Integrity Check
- Low-Level Implementations (cryptographic primitives implementations)
- Engines Provider – A shim that allows existing engines to work when called via the Core.
- Legacy Provider – Provides implementations of older algorithms that will be exposed via EVP-level APIs
- 3rd Party Providers
The FIPS 140-2 standard defines security requirements for cryptographic modules, and the last testing will occur on September 22, 2021, after which only validations against FIPS 140-3 will be performed according to NIST website. So time is running short to meet the deadline for OpenSSL 3.0, and the developers expect the certificate to only be delivered sometime next year.
The announcement also says the documentation has been greatly improved with a 94% increase in the amount of documentation since OpenSSL 1.1.1. An example is the design documentation for OpenSSL 3.0.0 that describes the architecture and features of the library.
OpenSSL 1.1.1 or earlier versions were released under a dual OpenSSL and SSLeay license, but the project has now (announced in 2017) switched to a standard Apache 2.0 license which means the project can be used for commercial and non-commercial purposes. This was already the case for the earlier license, but the move is said to encourage the use of OpenSSL in more open source projects since the Apache 2.0 license is widely used in the software industry.
You can download the source code and integrate it into your code, but note that since OpenSSL 3.0 is a major release, it is not fully backwards compatible with the previous OpenSSL 1.1.1 release. Nevertheless, the developers still expect most applications will still work unchanged and simply need to be recompiled.
Via Phoronix

Jean-Luc started CNX Software in 2010 as a part-time endeavor, before quitting his job as a software engineering manager, and starting to write daily news, and reviews full time later in 2011.
Support CNX Software! Donate via cryptocurrencies, become a Patron on Patreon, or purchase goods on Amazon or Aliexpress





Good. FIPS 140-2 is often an item on corporate buyers check list.