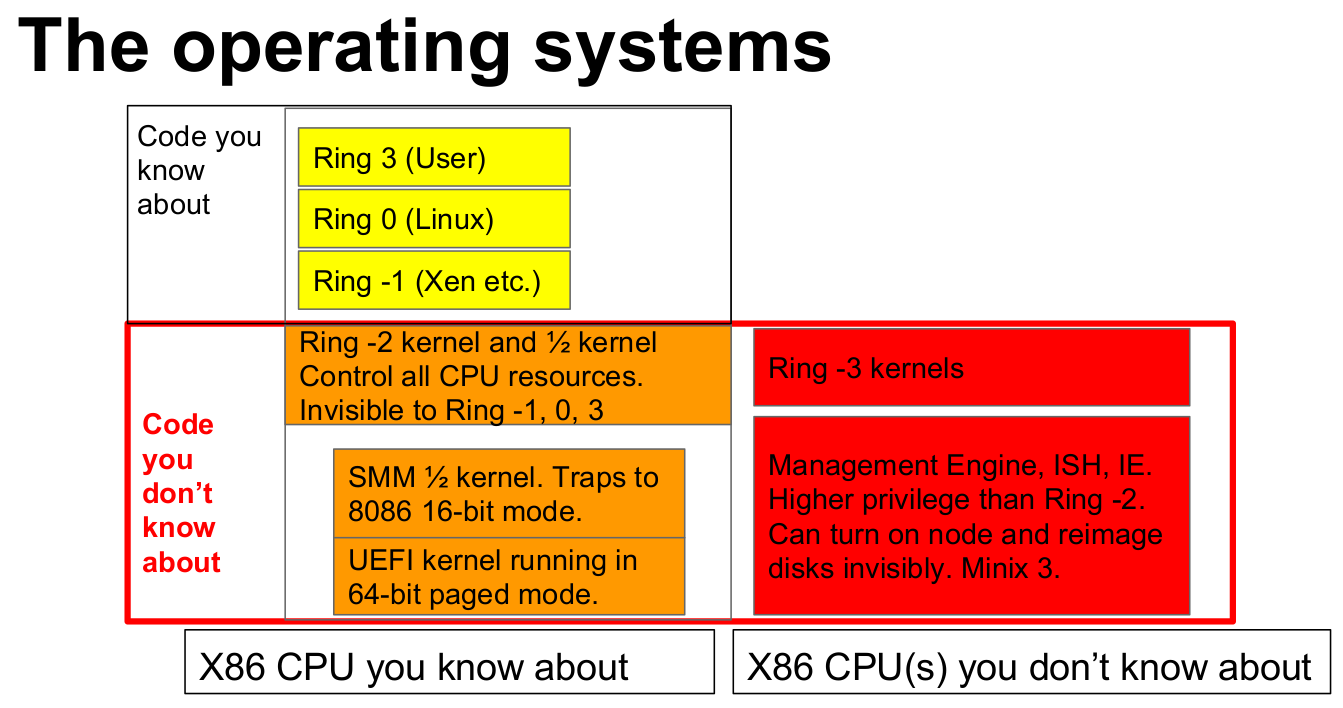
You may have heard a few things about Intel Management Engine in recent months, especially as security issues have been found, the firmware is not easily upgradeable, and the EFF deemed it a security hazard asking Intel for ways to disable it. In recent days, I’ve seen several media reports about the Management Engine being based on an Intel Quark x86-based 32-bit CPU running MINIX open-source operating system. Keep in mind, there’s nothing nefarious about MINIX, it’s just that Intel keeps its own developments on top closed. One of sources for the information is a blog post explaining how to disable Intel ME 11, but ZDNET also points to one of the talks at the Embedded Linux Conference Europe 2017 entitled “Replace Your Exploit-Ridden Firmware with Linux” by Ronald Minnich, Google which explains the problem, and proposes a solution to (almost) disable Intel’s ME, and replace UEFI by a small […]
Learn More About Linux’s New GPIO User Space Subsystem & Libgpiod
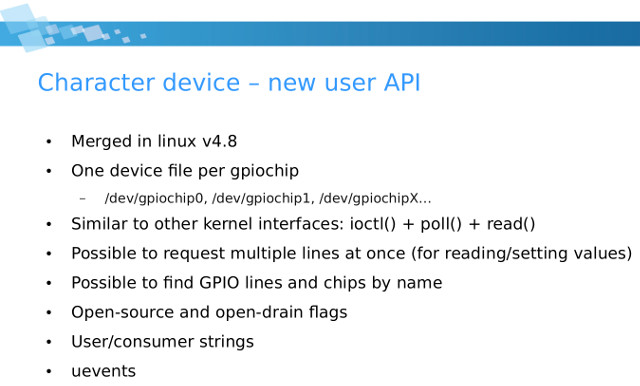
Sysfs was used to control GPIOs on Linux system with the GPIOs defined in /sys/class/gpio, but starting with Linux 4.8, a new GPIO interface for user space was introduced, with gpiochip becoming char devices foudn in /dev/gpiochip0, dev/gpiochip1, etc.. , and sysfs allegedly become deprecated. But a quick check in NanoPi Duo with Linux 4.11 shows both GPIO user space interfaces appear to be enabled:
|
1 2 3 4 |
ls /sys/class/gpio/ export gpiochip0 gpiochip352 unexport ls /dev/gpiochip gpiochip0 gpiochip1 |
Nevertheless overtime, sysfs will die out, and the new subsystem will likely be used by all systems, so it might be useful to learn more about it. One way to do that is to watch Bartosz Golaszewski’s ELCE 2017 talk entitled “New GPIO Interface for User Space” with the video embedded below. But I first I’ll summarize some of the key points. Now GPIO handling from user space becomes similar to other char driver with ioctl, poll and read functions, and beside assigning numbers […]
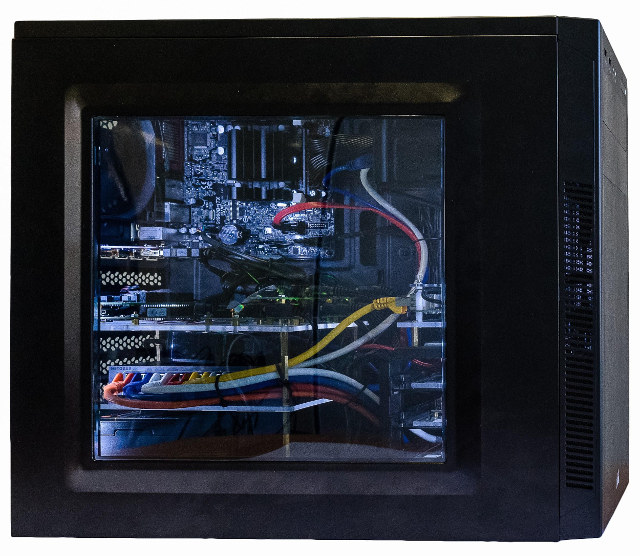
Lab in a Box Concept Embeds x86 Server and 6 ARM Boards into a PC Case for Automated Software Testing
The Linux kernel now has about 20 millions line of code, Arm has hundreds of licensees making thousands of processors and micro-controllers, which end up in maybe hundreds of thousands of different designs, many of which are not using Linux, but for those that do, Linux must be tested to make sure it works. The same stands true for any large software used on multiple hardware platforms. Manual testing is one way to do it, but it’s time consuming and expensive, so there are software and hardware continuous integration solutions to automate testing such as Linaro LAVA (Linaro Automated Validation Architecture), KernelCI automated Linux kernel testing, and Automotive Grade Linux CIAT that automatically test incoming patch series. Both CIAT and KernelCI focus on Linux, and rely on LAVA, with KernelCI leveraging hardware contributed by the community, and proven to be effective as since it’s been implemented, failed build configs dropped […]
Embedded Linux Conference & Open Source Summit Europe 2017 Schedule
The Embedded Linux Conference & IoT summit 2017 took place in the US earlier this year in February, but there will soon be a similar event with the Embedded Linux Conference *& Open Source Summit Europe 2017 to take up in Europe on October 23 – 25 in Prague, Czech Republic, and the Linux Foundation has just published the schedule. It’s always useful to find out what is being discussed during such events, even if you are not going to attend, so I went through the different sessions, and compose my own virtual schedule with some of the ones I find the most interesting. Monday, October 23 11:15 – 11:55 – An Introduction to SPI-NOR Subsystem – Vignesh Raghavendra, Texas Instruments India Modern day embedded systems have dedicated SPI controllers to support NOR flashes. They have many hardware level features to increase the ease and efficiency of accessing SPI NOR […]