We covered the Matter 1.3 specification in May 2024, but the Connectivity Standards Alliance is wasting no time and the Matter 1.4 specification is already out with features and improvements such as “Enhanced Multi-Admin”, Matter certifiable Home Routers and Access Points, energy management enhancements, and several new device types such as solar power equipment and batteries. Matter has been deployed in millions of Smart Home products in just a few years and aims to enable interoperability between devices from multiple vendors. Paisit reviewed a few Matter products from SONOFF including the MINIR4M Smart Switch, SONOFF Zigbee Bridge Ultra, and SwitchMan M5 Matter wall switch, and while Matter interoperability is working since devices can be controlled from Matter-compatible apps (e.g. Apple Home), users do lose some features found in the “native” app such as eWelink in the case of SONOFF devices. Matter 1.4 key improvements and new features: Home Routers and […]
Android 15 runs on Linaro development boards based on Qualcomm and HiSilicon chips
Android 15 source code was just pushed to AOSP last week, and Linaro has already ported it to four reference development boards based on Qualcomm and HiSilicon/Huawei chips namely Snapdragon 8 Gen 2 devboard (SM8550-HDK), Qualcomm Robotics Board RB5, Qualcomm Dragonboard 845c (DB845c, aka RB3) and HiSilicon Hikey960. Recent Google Pixel phones can already get Android 15 beta, but that makes the aforementioned development boards some of the first hardware platforms running Android 15 which could be useful to app developers and people wanting to customize Android 15 OS for their target product(s). Android 15 worked on the same day as the release to AOSP thanks to a collaboration between Linaro and Google to make sure reference boards get support as soon as possible, and in this case, we had a “0-day boot” as Linaro puts it. This collaboration started in 2022 with Qualcomm Robotics RB3 and RB5 platforms getting […]
Arduino CLI 1.0 released – Let’s try it with the Raspberry Pi Pico 2
Arduino has just announced the release of the Arduino CLI version 1.0.0, the first stable release for which users and developers can be confident the software API won’t change over time, or at least with minimal changes that will not impact the workflow of applications based on it. We first looked at the Arduino CLI when it was still at the alpha stage way back in 2018. Arduino CLI version 1.0.0 was actually quietly released about two months ago, but Arduino only announced it now and the utility is now at version 1.0.4 with several bug fixes. Arduino CLI 1.0 release The goal of the API is to easily program the boards from the command line without having to use the Arduino IDE, and the CLI can be integrated into your own script to automatize various processes. Arduino explains there are three ways to integrate and utilize the capabilities of […]
Android 15 source code pushed to AOSP
Android 15 will only become available on supported Pixel devices in the coming weeks, and on other phones in the next couple of months, but Google has already pushed Android 15 source code to AOSP (the Android Open-Source Project). We already documented some of the main changes in Android 15 when the first developer preview was released in February 2024. These included improvements related to privacy and security, the addition of the partial screen-sharing feature, camera and audio improvements, and some performance optimizations. You should be able to retrieve the Android 15 source code from AOSP with the following commands:
|
1 2 |
repo init --partial-clone -b android-15.0.0_r1 -u https://android.googlesource.com/platform/manifest repo sync -c -j8 |
Android 15 is based on Linux 6.6 LTS, so Android 15 SDKs from silicon vendors will likely be offered with Linux 6.6, although I can see Linux 6.1 is also an option. It’s also possible to browse Android 15 source code without downloading several GB of data to your […]
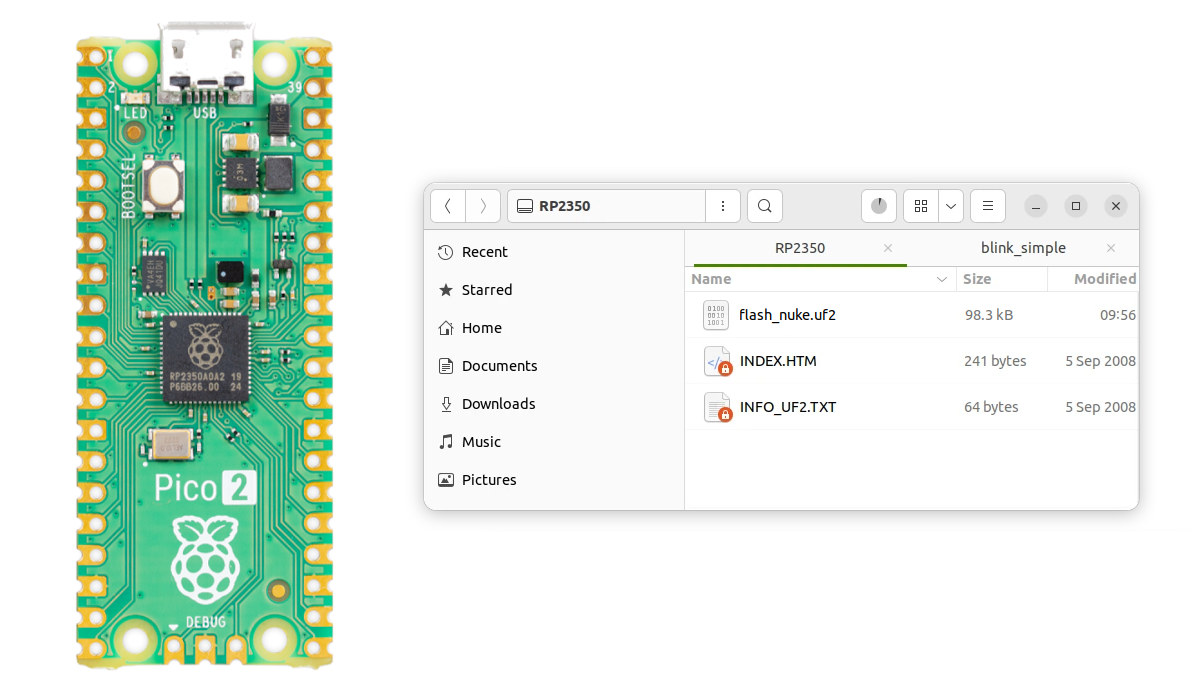
How to recover a “bricked” Raspberry Pi Pico 2 or other RP2350 board
In theory, it’s close to impossible to brick your Raspberry Pi Pico 2 or other RP2350 boards because the bootrom code (source code) is stored in the 32KB ROM of the microcontroller and is by definition “read-only memory”. But I managed to “brick” my Raspberry Pi Pico 2 the other day, and even a blinky sample would not run on the board. So I’ll explain a simple method to recover/perform a factory reset of sorts. First, let me explain what happened. My board became unusable after I ran the following command while building RISC-V Linux for RP2035 and my Pico 2 was connected to the build machine:
|
1 |
make flash-kernel |
At some point, it will copy a UF2 firmware binary designed for boards with PSRAM which the Raspberry Pi Pico 2 lacks:
|
1 |
cp build/psram-bootloader.uf2 "/media/jaufranc/RP2350"/ |
After that, I could still see the Raspberry Pi Pico 2 board as an “RP2350” drive on my computer, […]
DietPi 9.7 and Armbian 24.8 released with improved support for Rockchip, Amlogic, and Allwinner SBCs
Armbian and DietPi are two separate projects that provide Linux-based OS images optimized for Arm-based single board computers. The last time we had a look at both projects was in June with the release of Armbian 24.5.1 and DietPi 9.4, but there have been several updates since then including the releases of the latest DietPi 9.7 and Armbian 24.8 Yelt just a few days ago. So let’s check out the latest changes. DietPi 9.7 DietPi is a lightweight Debian-based Linux distribution for SBCs and server systems that ships as a minimal image but users can install any packages they want, including the ones required for desktop environment, to match the requirements of the applications. It’s notably used by the Linamp project – a Raspberry Pi 4-based project that brings WinAMP to real life – that we covered a few weeks ago. DietPi 9.7 was released on August 25, 2024 with […]
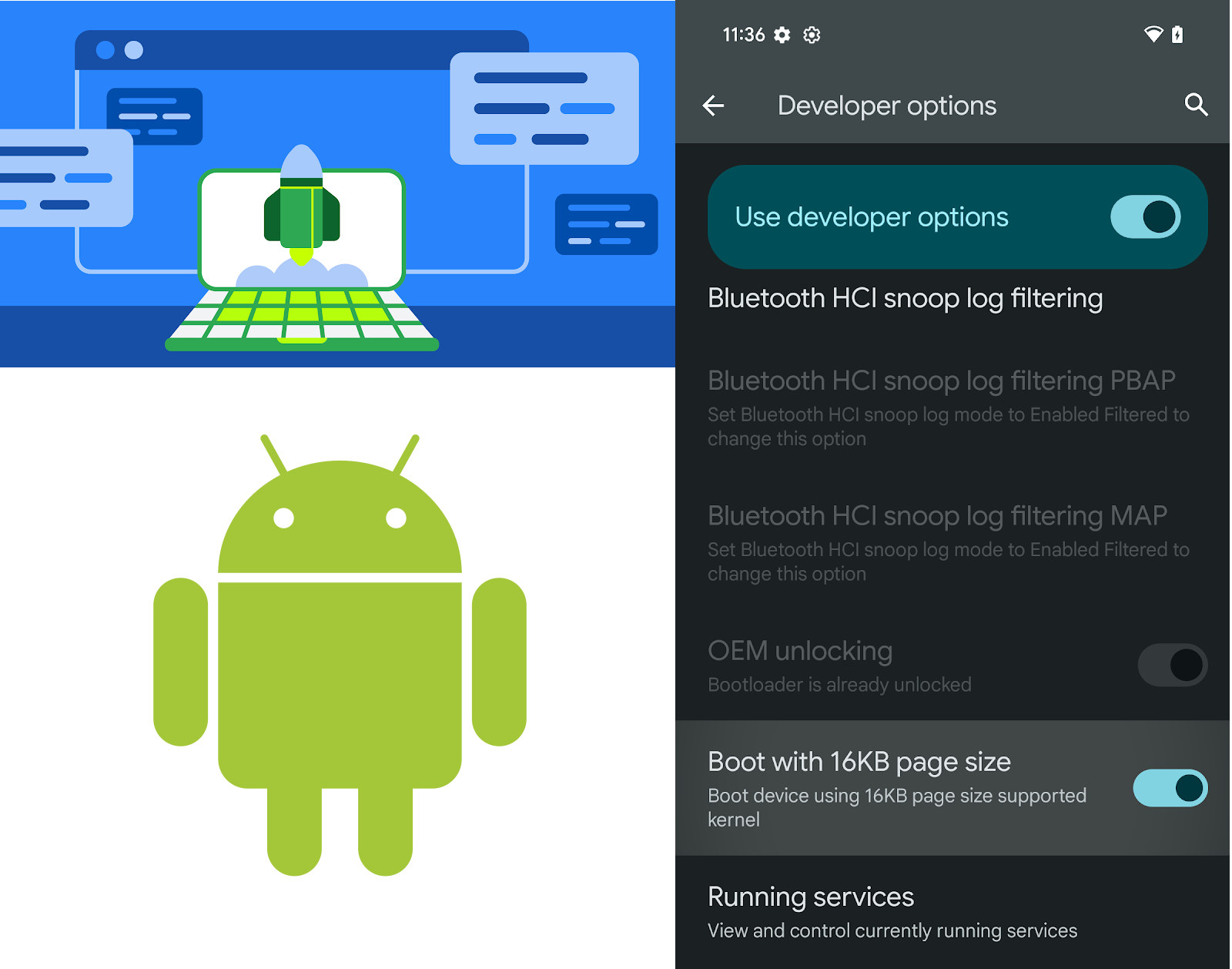
Android support for 16KB page size boosts performance by up to 10 percent
Most operating systems are set to use a 4KB page size since that’s what most CPUs support, but Android is often running on Arm CPUs that can support 16KB page size. So Google decided to enable 16 KB page size as a developer option in selected Android devices since it can deliver a 5 to 10% boost in performance, at the cost of using around 9% extra memory. Contrary to 32-bit/64-bit mode, a page size is not an Application Binary Interface (ABI), so once an application is fixed to be page size agnostic, it can run on both 4 KB and 16 KB devices without modifications. Apps written with Java or Kotlin don’t need modifications, but those that use native code (C/C++) or dependencies must be recompiled for compatibility with 16 KB page size devices. Google provides some details about the benefits of 16 KB page sizes on the developer […]
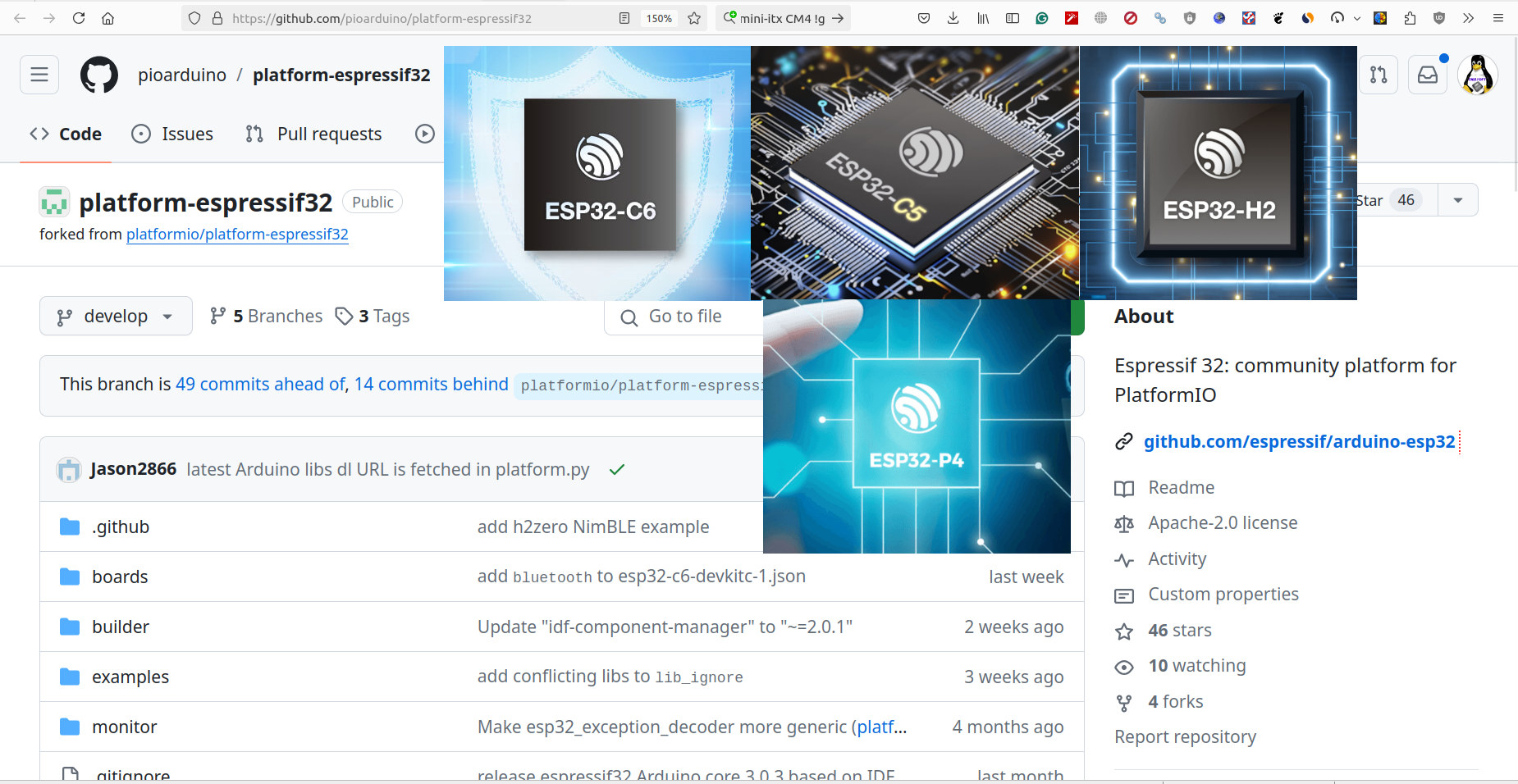
platform-espressif32 fork to enable PlatformIO support for ESP32-C6, ESP32-C5, ESP32-H2, and ESP32-P4 SoCs
When Espressif Systems released Arduino ESP32 Core 3.0.0 we noted that PlatformIO support was in doubt due to business issues between Espressif and Platform IO developers. There has been no progress since then, and PlatformIO is not even reviewing or merging community contributions to their platform-espressif32 library. So if you want software that’s officially supported by Espressif, you should stick to the Arduino ESP32 Core. But if you are a fan of PlatformIO for ESP32, there’s hope even for the newer chips like ESP32-C6, ESP32-H2, and ESP32-P4 among others, as pioarduino community members have now forked the platform-espressif32 library to keep the project alive. Users can still rely on the official PlatformIO repository for existing ESP32 boards and microcontrollers, but new ESP32-C6, ESP32-H2, ESP32-C5, ESP32-H4, and ESP32-P4 SoC will only be supported by the fork. pioarduino which stands for “people initiated optimized arduino” will maintain the fork, and currently, Arduino […]