The FlippenHeimer is a compact Geiger counter add-on module designed to work with the Flipper Zero. It allows users to monitor beta and gamma radiation levels using the Flipper’s display and power source, making it a portable device to detect radiation. Built around a J305 Geiger–Müller tube, the FlippenHeimer provides real-time data logging, visual feedback via graphs. Other than that, it features “atomic dice roller” functionality that uses the random nature of radioactive decay to generate unpredictable outcomes. Key components of this device include 555 timers, LM358 op-amps, 2N3904 and MPSA42 transistors, inductors, and high-voltage capacitors. These features make this device useful for applications such as environmental awareness, hobbyist radiation monitoring, and generating random values. FlippenHeimer Specifications: Main interface – Connects to Flipper Zero via GPIO/UART (plug-and-play with GPIO header) Detection device – J305 Geiger-Müller glass tube, suitable for gamma and beta radiation Radiation detection: Detects beta and gamma radiation […]
Antenna hack more than doubles the range of cheap ESP32-C3 USB-C boards
There are plenty of small ESP32-C3 IoT boards with a USB-C connector on the market, and while they all look very similar, antenna designs differ, and less thought-out ones may severely impact the WiFi and Bluetooth range. Peter Neufeld decided to hack one of those cheap ESP32-C3 boards by adding a custom antenna, and this resulted in the board having more than twice the range and almost three times in some cases. Those tiny boards are cramped, so there’s very little space around the ceramic antenna typically used, leading to poor RF performance. To work around that issue, Peter added a 31mm long antenna made of silver-plated wire, making a loop of about 8mm in diameter outside of the board and soldered on the ceramic antenna’s solder joints, and the rest of the wire (about 15mm) points upwards. As you can see from the photo above, he didn’t remove the […]
Flipper Blackhat is a Flipper Zero dual-band Wi-Fi card with an Allwinner A33 processor
Developed by Rootkit Labs in Switzerland, the Flipper Blackhat is an open-source Allwinner A33-based Flipper Zero dual-band Wi-Fi card running Linux and designed for penetration testing, cybersecurity research, and wireless network analysis. Built around an Allwinner A33 quad-core 1.5GHz processor, it comes with 1GB RAM, and an onboard 2.4GHz WiFi radio (RTL8723DS), with additional connectivity via two USB-A ports and one USB-C (FTDI-connected). The package also includes a 5GHz USB WiFi dongle (RTL8821CU) and a WiFi antenna for the built-in radio but requires an SD card and Flipper device separately. Flipper Blackhat Specifications: SoC – Allwinner A33 CPU – Quad-core Arm Cortex-A7 processor GPU – Arm Mali-400 MP2 VPU – 1080p60 H.264, VP8, MPEG 1/2/4, JPEG/MJPEG video decoding 1080p60 H.264 video encoding Memory – 1GB RAM Storage – SD Card slot Wireless Connectivity Realtek RTL8723DS 2.4 GHz Wi-Fi Includes Realtek RTL8821CU 5 GHz USB Wi-Fi dongle Supports additional third-party Wi-Fi […]
FlipMods Combo is a 3-in-1 Flipper Zero expansion module with ESP32, GPS, and CC1101 modules
Sacred Labs’ FlipMods Combo is a 3-in-1 expansion module for the Flipper Zero that combines an ESP32 WiFi and Bluetooth SoC, Texas Instruments CC1101 Sub-GHz wireless microcontroller, and an unnamed GPS module. The expansion module is housed in a neat 3D-printed case and features a built-in GPS antenna, external WiFI/Bluetooth & Sub-Ghz antennas, as well as a switch to send the GPS data to the ESP32 chip or the Flipper Zero. The ESP32 module is preloaded with the Marauder firmware also used in the ESP32 Marauder Pocket Unit and Mayhem v2 for Flipper Zero for penetration testing with Wi-Fi scanning, de-authentication attacks, packet sniffing, and more. FlipMods Combo specifications: Wireless modules ESP32-WROOM-32UE for WiFi and Bluetooth; external SMA antenna (long) Texas Instruments CC1011 for 315, 433, 868, and 915MHz ISM bands; external SMA antenna (short) GPS module with internal antenna Storage – MicroSD card slot up to 32GB USB – […]
Flipper Zero hacking tool gets MicroPython support
Developer and engineer Oliver Fabel has developed a port that is designed to run MicroPython on the Flipper Zero. This port allows users to write programs for Flipper Zero in Python, instead of built-in JavaScript. Till now you can access GPIO, ADC, PWM, the speaker, buttons, the display, and infrared communication with this but it doesn’t have support for NFC or RFID yet, and it’s still under development. Previously we have written about various addon boards for the Flipper Zero like the Mayhem v2, the ESP8266 Deauther board, the CAN bus addon board, and other powerful alternatives of the Flipper like The M1 and the HackBat. Feel free to check those out if you are interested in the topic. The process is simple, and you don’t have to do a firmware update to work with MicroPython, you can download the application from the community-driven Flipper app store and are good […]
Mayhem v2 expansion for Flipper Zero adds Wi-Fi, BLE, camera, microSD card slot, and NRF24 or CC1101 radio support
Erwin Ried‘s Mayhem v2 is an all-in-one ESP32 and NRF24L01-based expansion board designed for Flipper Zero. This board adds Bluetooth and Wi-Fi through an ESP32-S module, features 2MP camera with flashlight, a microSD card slot, and support for either an NRF24L01 module (for sniffing and mousejacking) or a CC1101 module (for external radio communication). These features make this Flipper Zero add-on board useful for WiFi and Bluetooth penetration testing, motion detection, QR code reading, and as a nanny cam with remote access. Previously we have written about similar expansion boards like the Flipper Zero ESP8266 Deauther which adds de-authentication capabilities and the Flipper Add-On CANBus which can be used to sniff, send, and log CAN bus packets directly from the Flipper Zero. Feel free to check those out if you are interested in those tools. Mayhem v2 Flipper Zero add-on board specification Wireless Module – ESP32-S WiFi 802.11 b/g/n + […]
nRFBOX V2 ESP32 wireless hacking tool can scan, analyze, spoof, and jam the whole 2.4GHz spectrum
CiferTech has recently introduced the nRFBOX V2 ESP32-based wireless hacking tool designed for spectrum analysis, jamming, BLE device emulation, and more. The device is built around an ESP32-WROOM-32U module and includes an NRF24 module covering the whole 2.4GHz spectrum. Additionally, the device has a 0.96-inch OLED display, a five-way microswitch control pad, and a WS2812 RGB LED for feedback. The device can also be operated with a single 3.7V lithium battery, and that batter’s charging is handled by a TP4056 charging IC. All these features make this device useful for wireless security testing, educational environments, research, and hobbyist projects. Previously we have written about similar portable hacking tools like the DSTIKE Deauther Watch X, the HackBat pen-testing device, and the popular Flipper Zero wireless hacking tool. Feel free to check those out if you are looking for similar products. nRFBOX V2 specifications Microcontroller – ESP32-WROOM-32U with ESP32 dual-core wireless microcontroller […]
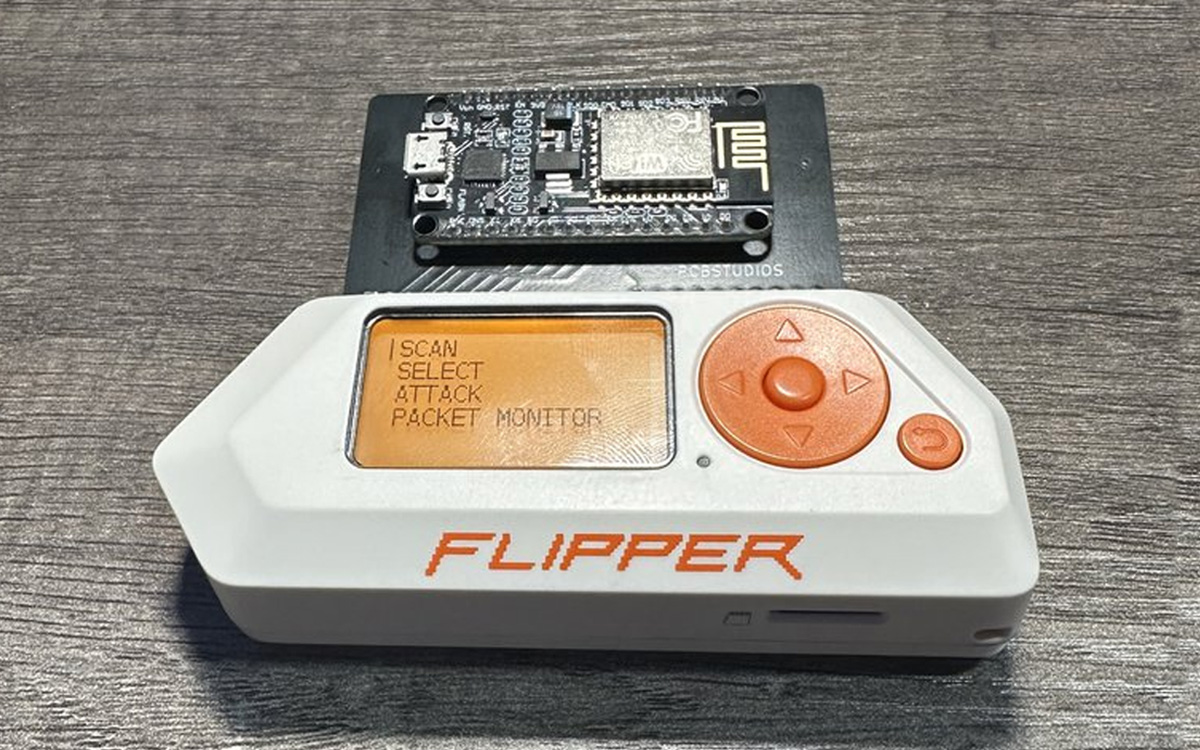
Flipper Zero hacking tool gets ESP8266 Deauther add-on for Wi-Fi security and research
PCB Studios has just launched the “Flipper Zero ESP8266 Deauther” adapter board for Flipper Zero that enables users to conduct de-authentication attacks on Wi-Fi networks. Running a modified version of SpacehuhnTech’s ESP8266 Deauther software, this board has a variety of actions for testing 802.11 wireless networks. Its primary function, deauthentication, sends deauthing packets to the target network, disconnecting devices from their 2.4 GHz Wi-Fi networks. In our last post about Flipper Zero, we wrote about Flipper Add-On CANBus a CAN bus hacking tool that can sniff, send, and log CAN bus packets. Other than that we have seen similar tools like the M1 multitool and HackBat which can be considered as Flipper Zero alternatives with STM32H5 and Raspberry Pi RP2040 MCUs and Wi-Fi connectivity. We have also written about various ESP8266 and ESP32-based Deauther tools like the DSTIKE Deauther Watch X, the Cheap Evil Tech Deauther board, and ESP32 Marauder […]