The Embedded Systems Conference took the name “Design West” for a couple of years, but this year, there’s no mention of Design West, and the Embedded System Conference 2015 will take place in Boston, MA, US on May 6-7, 2015. The 2-day event will have a demo hall, and well as sessions divided into 8 tracks: Connected Devices and the IoT Embedded Software Design Hardware: Design, I/O and Interfacing Prototyping Embedded Systems Design Software: Design, Languages, & Quality Fantastical Theater Teardowns The full schedule has now been posted, and I’ll build a virtual schedule with some of the sessions provided. Wednesday May 6, 2015 8:00 – 8:45 – Understanding Google/Nest Thread by Michael Anderson, Chief Scientist, The PTR Group, Inc. The IoT will live or die based on its connectivity. In examining existing wireless protocols, Google/Nest found most of them lacking. In order to address the needs for low-power wireless […]
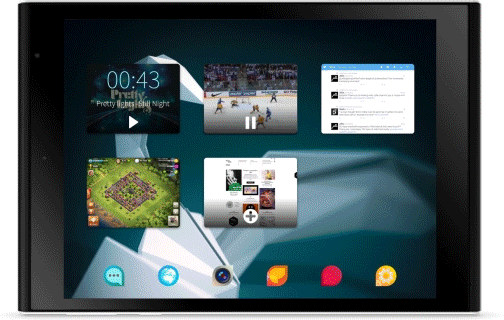
Jolla Opens Sailfish OS 2.0 for Licensing, Unveils Sailfish Secure, Plans Atom x3 Support
As the Jolla Tablet running Sailfish OS 2.0 is about to ship to Kickstarter backers (Q2 2015), the company has issues a press release announcing Sailfish OS 2.0 is now ready for licensing to OEMs and other partners, and OS porting is being done to the newly announced Intel Atom x3 processors. Sailfish OS 2.0 has been designed for both smartphones and tablets with the following key changes and improvements: Stronger technical OS core and improved Android application compatibility Support for Intel architecture, including the Intel Atom x3 processor Best multitasking on the market for both smartphones and tablets Improved user experience with an enhanced, even richer user interface Strong privacy and personalization features Many new UI/UX features, like enhanced notifications and events views, and even simpler swipe access to main functions Sailfish 2.0 is designed to provide premium visibility in the UI for leading digital content providers and to […]
FOSDEM 2015 Schedule – January 31 – February 1 2015
FOSDEM (Free and Open Source Software Developers’ European Meeting) takes place every year during the first week-end of February. This year the developer-oriented event expects to bring over 5000 geeks to share ideas and collaborate on open source projects. Contrary to most other events, it’s free to attend, and you don’t even need to register, just show up. FOSDEM 2015 will take place on January 31- February 1 in Brussels. There will be 551 sessions divided into 5 keynotes, 40 lightning talks, 6 certification exams, and with the bulk being developer rooms and main tracks, divided into 7 main tracks this year: Languages, Performance, Time, Typesetting, Hardware, Security and Miscellaneous. I’m not going to attend, but it’s still interested to see what will be talked about, and I’ve concocted my own little virtual program out of the main tracks and developers’ rooms. There’s a few minutes overlap between some talks […]
Linaro Connect Hong Kong 2015 Schedule and Demos
Linaro Connect Hong Kong 2015 will take place on February 9 – 13,2015 in Hong Kong, and the organization has released the schedule for the five days events with keynotes, sessions, and demos. Each day will start with the keynote including speakers such as: George Grey, Linaro CEO, who will welcome attendees to Linaro Connect, and provide an update on the latest Linaro developments Jon Masters, Chief ARM Architect, Redhat, who will present Red Hat update and latest ARMv8-A demonstrations Dejan Milojicic, Senior Researcher & Manager, HP Labs Bob Monkman, Enterprise Segment Marketing Manager, ARM, will discuss about the impact of ARM in next generation cloud and communication network infrastructure Greg Kroah-Hartman, Linux Foundation Fellow, will introduce the Greybus Project (Linux for Project Ara modular phones) Warren Rehman, Android Partner Engineering Manager, Google The agenda also features sessions covering Android, ARMv8-A, Automation & Validation, Digital Home, Enterprise Servers, LAVA, Linux […]
Linux 3.18 Released
Linus Torvalds released Linux Kernel 3.18 last Sunday: It’s been a quiet week, and the patch from rc7 is tiny, so 3.18 is out. I’d love to say that we’ve figured out the problem that plagues 3.17 for a couple of people, but we haven’t. At the same time, there’s absolutely no point in having everybody else twiddling their thumbs when a couple of people are actively trying to bisect an older issue, so holding up the release just didn’t make sense. Especially since that would just have then held things up entirely over the holiday break. So the merge window for 3.19 is open, and DaveJ will hopefully get his bisection done (or at least narrow things down sufficiently that we have that “Ahaa” moment) over the next week. But in solidarity with Dave (and to make my life easier too 😉 let’s try to avoid introducing any _new_ […]
Linaro 14.11 Release with Kernel 3.18, Android 5.0, & Ubuntu Utopic. Debian 8.0 Gets ARM64 Port
Linaro 14.11 has been released with Linux kernel 3.18-rc5 (baseline), Linux 3.10.61 & 3.14.25 (LSK, same versions as last month), and Android 4.4.2, 4.4.4, and for the first time Android 5.0 Lollipop. There’s also been some news with regards to Linux desktop distributions, as Ubuntu baseline has been upgraded to Utopic (14.10), and Debian 8.0 (Jessie) will officially support ARM64 with 93% of packages built as of November 5th. Android Lollipop images are said to be built for TC2, Juno, Nexus 7, Nexus 10, and FVP models, but I could not find the images. Finally, it’s the first time I’ve noticed Hisilicon X5HD2 development board with a dual core Cortex A9 processor, but apparently it’s the same as Hi3716cv200. Here are the highlights of this release: Linux Linaro 3.18-rc5-2014.11 updated GATOR to version 5.20 updated topic from Qualcomm LT (include IFC6410 board support) updated integration-linaro-vexpress64 topic by ARM LT (FVP […]
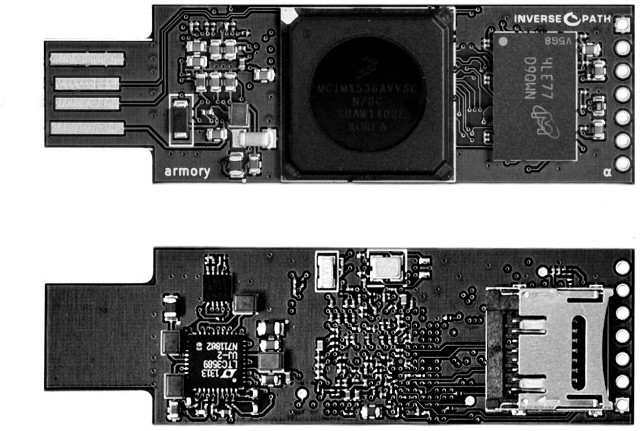
USB Armory is an Open Source Hardware Freescale i.MX53 Dongle for Security Applications
Most computers-on-a-stick come with an HDMI port, and a few USB ports, but Inverse Path’s dongle is quite different. USB Armory is a flash drive sized computer powered by Freescale i.MX53 Cortex A8 processor with only a USB port and a micro SD slot, that targets security applications such as mass storage devices with automatic encryption, virus scanning, host authentication and data self-destruct, VPN routers, electronic wallets, password managers, portable penetration testing platforms, and so on. USB Armory specifications: SoC – Freescale i.MX53 ARM Cortex-A8 @ 800Mhz with ARM TrustZone System Memory – 512MB DDR3 RAM Storage – microSD card slot USB – 1x USB host port. USB device emulation: CDC Ethernet, mass storage, HID, etc. Expansion Header – 5-pin breakout header with GPIOs and UART Misc – customizable LED, including secure mode detection Power – 5V via USB (<500 mA power consumption) Dimensions – 65 x 19 x 6 […]
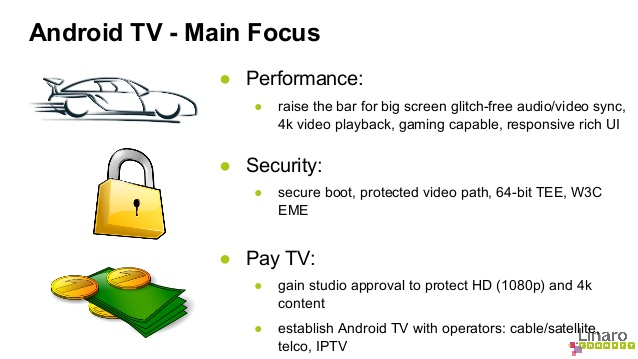
Android TV Overview – Linaro Connect US 2014
Google announced Android TV and ADT-1 devkit last June, as the company wants to bring user-friendly Android user-experience to TVs, set-top boxes and game consoles. Mark Gregotski, head of the Linaro Digital Home Group (LHG), has provided a technical overview of Android TV during the on-going Linaro Connect US 2014. You find a summary of yesterday sessions on Linaro’s blog, and the even will last until Friday, where several demos will be showcased. SoC companies currently involved in Android TV include Nvidia, Marvell, Qualcomm, Mediatek, Intel, Broadcom, and ST micro, so none of usual Chinese Android TV Box players (Rockchip, Amlogic, AllWinner…) are represented. Android (for smartphone) currently support video playback but you may experience dropped frame from time to time, where in the STB market requirements are not stringent. For example, NTT is said to only allow one frame dropped per month! So Android TV aims to improve video […]