Installing or upgrading packages in Linux distributions does not normally require rebooting your system, except for the Linux kernel and drivers. But since Linux 4.0 kernel, Live Kernel patching is possible, meaning Linux kernel updates can be performed without having to reboot your server or computer. Canonical is now taking advantage of this new feature with their Livepatch Service available for Ubuntu 16.04 LTS and greater.
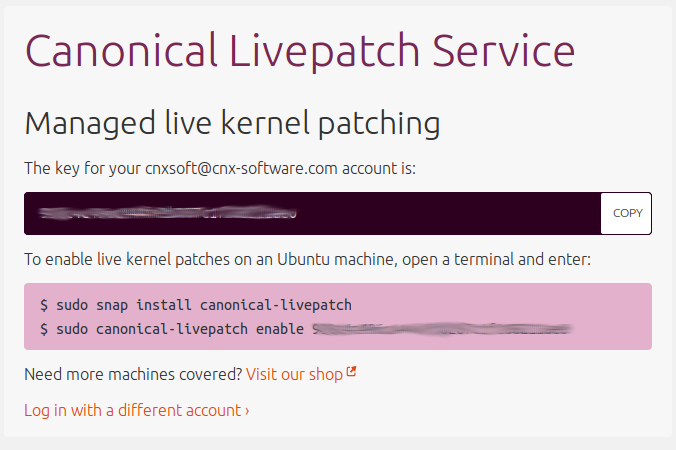 If you want to enable it on your machine, you’ll have to authenticate to Livepatch portal to get a key / token for the service as shown in the screenshot above.
If you want to enable it on your machine, you’ll have to authenticate to Livepatch portal to get a key / token for the service as shown in the screenshot above.
Now you can install the service:
|
1 |
sudo snap install canonical-livepatch |
and enable it with your token:
|
1 2 |
sudo canonical-livepatch enable [your-token] Successfully enabled device. Using machine-token: [your-token] |
That’s it. Your can check Livepatch service status with the command:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 |
canonical-livepatch status --verbose client-version: "5" machine-id: [your-machine-id] machine-token: [your-machine-token] architecture: x86_64 cpu-model: AMD FX(tm)-8350 Eight-Core Processor last-check: 2016-10-25T19:35:55.009247615+07:00 boot-time: 2016-10-25T09:00:09+07:00 uptime: 10h52m7s status: - kernel: 4.4.0-45.66-generic running: true livepatch: state: nothing-to-apply version: "" fixes: "" |
In my case, an update was not necessary, but if there’s one you should see something like:
|
1 2 3 4 |
livepatch: state: applied version: "12.2" fixes: '* CVE-2012-6828' |
That way you can make sure your system always have the latest security patchsets. This is mostly useful for servers, but it might not be a bad idea to enabled for your computer too, especially it’s free for end-users for up to 3 machines. Companies need to apply to Ubuntu Advantage for business to support more machines.

Jean-Luc started CNX Software in 2010 as a part-time endeavor, before quitting his job as a software engineering manager, and starting to write daily news, and reviews full time later in 2011.
Support CNX Software! Donate via cryptocurrencies, become a Patron on Patreon, or purchase goods on Amazon or Aliexpress. We also use affiliate links in articles to earn commissions if you make a purchase after clicking on those links.




Looks like a proprietary service.
Otherwise, fx8350 is a fast cpu?
I thought Ubuntu’s ‘snap’ was like docker, so it couldn’t do anything outside its container.
But now I see that with a snap package you can even patch the kernel of the host, so my assumption was apparently false.
The stuff explained in detail: http://blog.dustinkirkland.com/2016/10/canonical-livepatch.html
Closed source:
” The source code of the canonical-livepatch client is part of Canonical’s Landscape system management product and is commercial software”
@zoobab
If memory serves, livepatch builds on the common APIs of kpatch and kgraft that were originally developed and released separately in 2014 by Red Hat and Suse and were submitted for mainlining as a single common live patching core APIs in 2015. They’re FOSS implementations of ksplice (2008).
Currently, Arch and Ubuntu use livepatch, Suse uses kgraft and Red Hat Enterprise Linux uses kpatch. Features wise, kpatch and kgraft are on parity while livepatch is slightly lagging behind. Performance wise, kgraft is the fastest. However, kpatch is a little safer in theory.
Overall, there’s some kernel work going around to make live patching a bit more ubiquitous outside the x86 world.
Does it work on ARM as well?
@zoobab
If it works it should only work on officially supported ARM images for servers -> https://www.ubuntu.com/download/server/arm
It does not work for most ARM platforms, nor Intel Bay Trail/Cherry Trail hardware.
@Sander
I see snap as an eventual replacement for apt / apt-get.
@zoobab
Finally, It won’t work on ARM:
@zoobab
FX8350 single thread performance is not that good, but I upgraded mostly when I need to run make to build things like the Linux kernel, Qt, and AOSP, and with eight cores it’s fast enough. It also consumes a lot of power (125W TDP). I hope in a few years I can buy a new desktop machine with a 10 to 15W ARM or Intel SoC with the same or greater performance.
@zoobab
Here is the launchpad page for the client, https://launchpad.net/canonical-livepatch-client
It is indeed closed-source.
The kernel livepatch functionality is available in the kernel, and what Canonical is providing is an easy/secure/tested way to apply those updates, on the stock Ubuntu kernel. Such a feature makes a lot of sense to paying customers that run servers.
It is always possible for someone to create on their own (for free) those livepatch updates and apply them.
So the users that join the free livepatch service are the beta-testers (“Once a livepatch passes CI/CD and regression tests, it’s rolled out on a canary testing basis, first to a tiny percentage of the Ubuntu Community users of the Canonical Livepatch Service.”) and if anyone ever wants to deploy a rootkit in critical infrastructure he’ll attack this proprietary service.
@tkaiser
+1 for a rootkit.
This locked-down proprietary crap with deep reach into the system you once thought YOU controlled is a honeypot for attackers. Canonical is not only stupid, they’re Evil!
@Drone
The funny thing is that this service targets service providers who want to minimize downtimes since they provide LXD containerization (Ubuntu Cloud): https://www.ubuntu.com/cloud/lxd
Since all containers share the same kernel it gets really interesting to attack such instances since one single rootkit owns a few hundred LXD instances or a few thousand Docker containers 🙂
In a world where people install devices in their households that send every spoken word or pictures/videos to the cloud who should wonder that there are proprietary services running inside the kernel securely communicating and receiving ‘patches’ from somewhere else. Madness everywhere 😉