Bootloaders takes care of the initial boot sequence on the hardware before the operating system takes over. For example, U-boot is often used in embedded systems as the bootloader before starting the main operating systems such as Linux or FreeBSD. MCUBoot is also a bootloader, but it targets the IoT, here referring to MCU based systems with limited memory and storage capacity, and is born out of work on Apache Mynewt OS, when developers decided to develop the bootloader separately from the operating system.
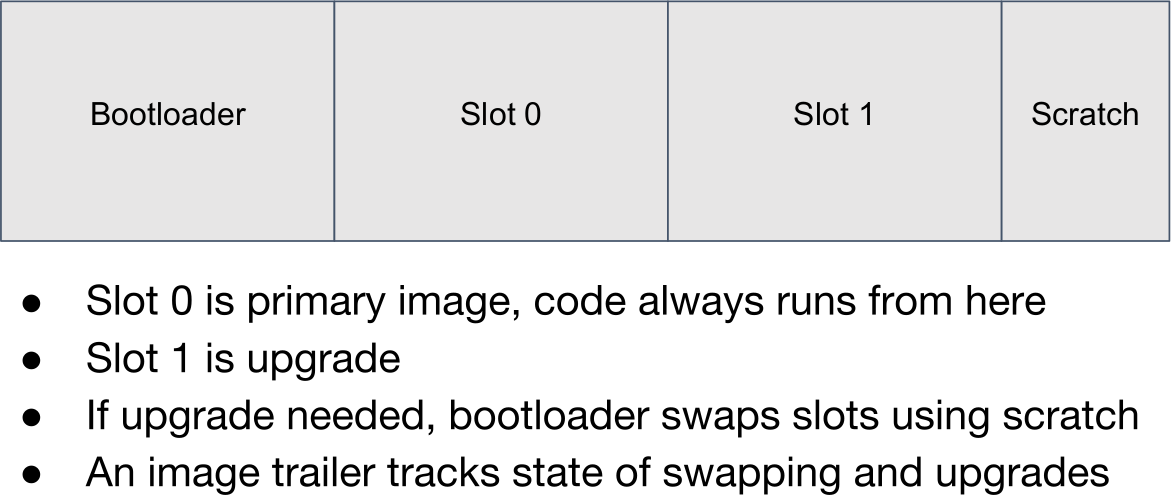
MCUBoot is designed to run on small & low cost systems running on MCU with ~512 KB flash, ~256 KB RAM, and currently supports Zephyr OS and Mynewt, with support for other RTOS also considered. Due to constraint the bootloader uses minimal features with a flash driver, a single thread, and crypto services. The project also aims at solving security and field firmware updates. To address the latter, the flash is partitioned in four sections, one for the bootloader, one “slot” with the primary image, a second slot for the firmware upgrade, and a Scratch partition to swap slots when an upgrade is needed. An image trailer at the end of each slot indicates the state of the slot.
You’ll find the source code in MCUBoot repository in Github, and you may want to watch the presentation at Linaro Connect Budapest 2017 for more details.

Jean-Luc started CNX Software in 2010 as a part-time endeavor, before quitting his job as a software engineering manager, and starting to write daily news, and reviews full time later in 2011.
Support CNX Software! Donate via cryptocurrencies, become a Patron on Patreon, or purchase goods on Amazon or Aliexpress. We also use affiliate links in articles to earn commissions if you make a purchase after clicking on those links.






How safe is it against NSA-Backdoor? Snowden told us, NSA can boot up our Mobile-phone even we had it “power off”.
There are things like “Wake on Lan” on our computer, okay PC´s have a Bios-Batterie for this, in a smartphone I don´t see such a batterie, but it must be possible, why should Edward lie?
> How safe is it against NSA-Backdoor?
The code itself is open source, so if people are concerned they can audit it. However as a consumer it’s not really practical to verify that your smart device is using the bootloader built from the GitHub source code.
> Snowden told us, NSA can boot up our Mobile-phone even we had it “power off”.
He is referring to the baseband, which is proprietary to each manufacturer (e.g. Qualcomm, Samsung, Hisilicon, etc) and which is closed source and (to my knowledge) has never been audited. So it’s completely unrelated to the above article.
> There are things like “Wake on Lan” on our computer, okay PC´s have a Bios-Batterie for this,
The BIOS battery has nothing to do at all with WOL. It is there to keep the real-time clock powered so your computer doesn’t lose the date and time if you unplug it from the wall.
> in a smartphone I don´t see such a batterie, but it must be possible, why should Edward lie?
If you remove the battery from a smart phone, there’s very little chance the NSA can turn it on. However this only works for phones with a removable battery, for phones with a built-in battery you just have to trust that it is off.
As long as there is a battery in the phone, it is possible the baseband could still be running.
Also, see the presentation at the most recent Embedded Linux Conference / OpenIoT:
https://www.youtube.com/watch?v=2p2i_hMDmgk&t=5s&list=PLbzoR-pLrL6pSlkQDW7RpnNLuxPq6WVUR&index=67
The presentation was in the context of Apache Mynewt as the MCUBoot project was transitioning, but very germane to the genesis and design decisions.
There are also three other presos around Apache Mynewt at ELC/OpenIoT around Build+Package Management; OIC 1.1/IoTivity-based management of constrained devices; the NimBLE BLE 4.2 stack:
https://www.youtube.com/watch?v=exfRbjMZbYk&index=61&list=PLbzoR-pLrL6pSlkQDW7RpnNLuxPq6WVUR
https://www.youtube.com/watch?v=ecKmSwdUIoo&index=88&list=PLbzoR-pLrL6pSlkQDW7RpnNLuxPq6WVUR
https://www.youtube.com/watch?v=TiIxC1QbZ3k&list=PLbzoR-pLrL6pSlkQDW7RpnNLuxPq6WVUR&index=27&t=3s
thanks 4 ur declartion, that’s why I prefere a dual-sim phone with changleable accu and expand-Memory-card , as a lonly knight…
Yes, I mean it serious, please take care, I´m not in that knowledge about source-listening, but here I hope some of readers, which do everything against backdoors!
Stop drugs