File Encryption is enabled – even required – by default in most Android devices, as it protects your data would you lose your phone, or have it stolen. Encryption in Android leverages the Advanced Encryption Standard (AES), and most modern 64-bit processors – like the ones based on Armv8 – come with a crypto accelerator that boosts performance several folds compared to a software only solution. But there are also many low end devices, for example based on Arm Cortex-A7, that lack crypto extensions, and enabling AES encryption would make the devices even slower than they already are.
So in order to provide file encryption on entry-level hardware without comprising too much on performance, Google has developed Adiantum encryption optimized to run on targets without crypto accelerator.
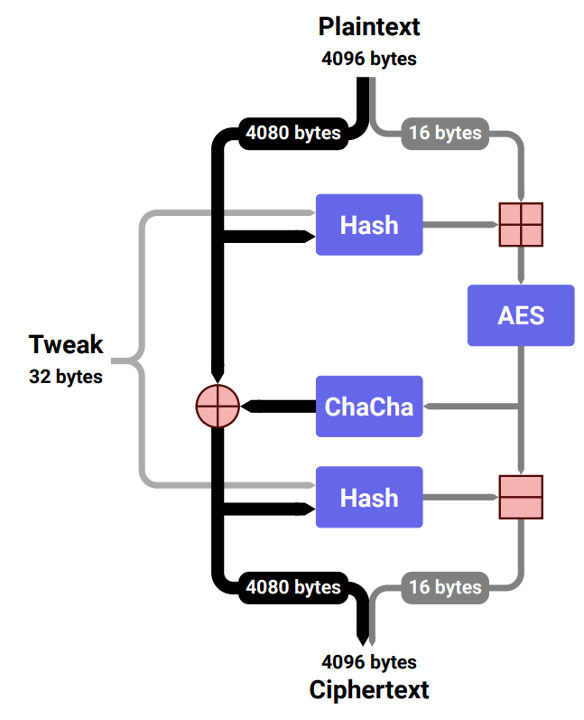
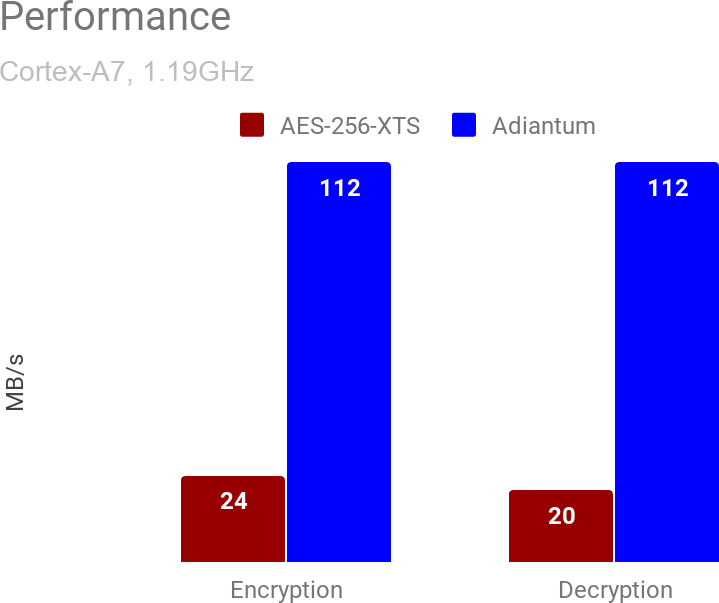
As explained in a Google Security blog post, Adiantum uses the ChaCha stream cipher – as used in HTTPS – in a length-preserving mode since file systems work in 4096 bytes block. The encryption further adapt ideas from AES-based proposals for length-preserving encryption such as HCTR and HCH. This results in much better efficiency on Arm Cortex-A7, with Adiantum encryption and decryption on 4096-byte sectors being around 10.6 cycles per byte, or 5x faster than AES-256-XTS.
The Arm optimized implementation of Adiantum can already be found in Android Linux 4.9 kernel, and will be found in Linux 5.0 mainline kernel. You can also find the source code of the reference implementation, test vector, and benchmarking suite of Adiantum on Github, and the new encryption/decryption mode can now be enabled by manufacturers in Android 9.0 or greater in devices unable to sustain 50MB/s AES file encryption/decryption. Note that Adiantum is still slower than AES in Arm & x86 devices with an AES crypto accelerator.

Jean-Luc started CNX Software in 2010 as a part-time endeavor, before quitting his job as a software engineering manager, and starting to write daily news, and reviews full time later in 2011.
Support CNX Software! Donate via cryptocurrencies, become a Patron on Patreon, or purchase goods on Amazon or Aliexpress. We also use affiliate links in articles to earn commissions if you make a purchase after clicking on those links.





That’s some proper engineering.
addresses one of the biggest flaws with armhf.