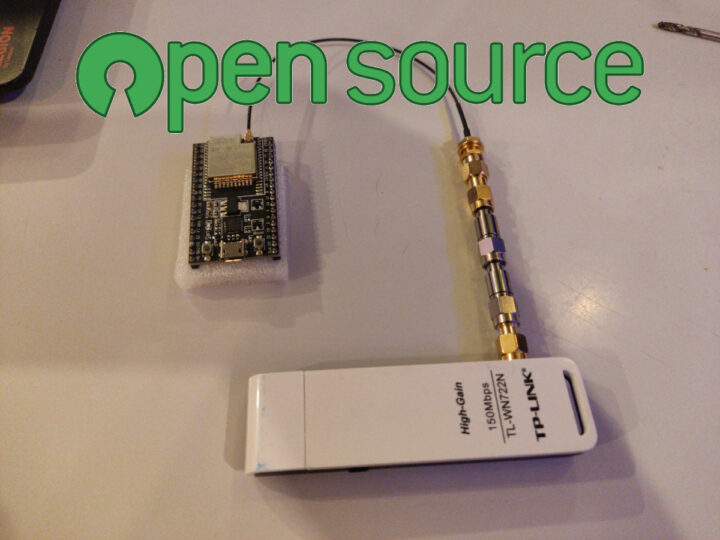
Most, if not all, WiFi hardware relies on closed-source binary blobs including ESP32 wireless MCU, but there’s now work underway to reverse engineer a WiFi MAC layer for the ESP32 to make it a truly open-source platform.
Espressif ESP32 wireless microcontrollers already have an open-source framework (ESP-IDF) and toolchain, people can customize the code to some extent, but this excludes the wireless bits (Wi-Fi, Bluetooth, low-level RF functions) that are distributed as closed-source precompiled libraries integrated into the firmware. There were some efforts to provide an open-source stack for the BL602 chip but it never went anywhere, and the ESP32 may become the first target with an open-source driver without any blobs, excluding FPGA-based projects such as OpenWiFi.
The early-stage implementation currently supports the following features:
- Sending WiFi frames
- Receiving WiFi frames
- Send an ACK packet as a reply to packets that are sent to the ESP32
- Connect to an open access point & send UDP packets
- Hardware packet filtering based on MAC address
Note that the initialization (setup) code still relies on the closed-source proprietary code, but that’s still good progress, Other features that should be implemented soon include switching channels, changing the data rate, adjusting Tx power, and implementing an open-source WiFi hardware initialization sequence. Once it’s done the driver will be integrated into an open-source 802.11 MAC implementation.
Longer term, the following features would be worked on:
- Modem power saving: turning off the modem when not in use
- AMSDU, AMPDU, HT40, QoS
- Cryptography needed for WPA2 done in hardware instead of in software
- Bluetooth support
- Write SVD documentation for all reverse-engineered registers. An SVD file is an XML file that describes the hardware features of a microcontroller and makes it possible to automatically generate an API from the hardware description.
The project will enable developers to introduce new features and could be especially useful for WiFi Mesh (IEEE 802.11s) since the current implementation by Espressif Systems is rather limited. If you want to find out more about the reverse-engineering work, read the relevant blog post by Jasper Devreker (that’s a long read), and you’ll find the source code on GitHub as well.
Thanks to Zoobab for the tip.

Jean-Luc started CNX Software in 2010 as a part-time endeavor, before quitting his job as a software engineering manager, and starting to write daily news, and reviews full time later in 2011.
Support CNX Software! Donate via cryptocurrencies, become a Patron on Patreon, or purchase goods on Amazon or Aliexpress





The source is closed due to FCC rules, not for vendor secrecy. If you had the source you could easily modify it to use illegal frequencies and power settings. To stop people from doing that the source is closed.
There is a famous case of someone hacking their wifi near the airport in San Juan PR and accidentally interfering with the planes during landing. Radio altimeter frequencies are near the wifi bands.
Thank god the world is more diverse than FCC.
And honestly, if someone wants to mess with radio altimeters there are dozens of other (legal) solutions to abuse, so nailing down WiFi HW is quite pointless.
There is no way to stop people from purposely messing with other bands. This rule is more about you unintentionally messing with other bands because you don’t realize the implications of the changes you made. That is what happened in PR, they had no clue they were messing with the radio altimeters.
Well how many people are messing with the sources of their drivers?
If you have a spectrum analyzer which can see 2.4Ghz and you hook it up and watch it, then it is probably ok to hack. But it you are hacking this without any way to observe what you are doing it can cause problems.
The dummies in PR tuned their radios outside the ISM band and then hooked up a power amp to get a nice, clear long range link. That worked and they got a nice link. Of course they did this in someone else’s frequency causing all kinds of interference since they were the strongest signal. They were lucky to only get a $25K fine and lose their equipment, no jail time.
Do the same thing in the 5Ghz wifi band and the owners of weather radars are going to hunt you down.
Agreed. There are thousands of other (legal) solutions to abuse.
And the FCC rules are valid where?
This is really great news, not so much if you want to use the espas a wifi mcu, but a completely documented, cheap, easily available RF IC in a good and proven quality certified module allows alot of use cases for “proprietary” RF HW outside of the ecosystem of beken and other cloned NRFs…