When I think about geolocation in I normally think about global navigation satellite systems such as GPS, GLONASS, Galileo, or Beidou, as well as IP geolocation, but the latter is highly inaccurate, and often only good for find out about the country, region, or city.
But if you’ve ever been into your phone location settings, you’d know GPS is only one option, as it can also leverage cellular base stations and WiFi SSIDs, where the former working where there’s coverage, and the later in area with a high enough density of access points. Somehow, I had never thought about using such technology to find location with WiFi modules until Espressif Systems released an application note entitled “Geolocating with ESP8266“.
This document describes how the ESP8266 module may be used to scan for nearby Wi-Fi access points and, then, use their SSID, RSSI and MAC address to obtain a potential fix on the device’s geolocation, using Google geolocation API.
That’s basically a two step process with an AT command returning the list of available APs, SSID, RSSI, and MAC Address:
|
1 2 3 4 |
AT+CWLAP +CWLAP:(2,"HotelFlower",-76,"c8:3a:35:b3:16:48",11,0,0) +CWLAP:(3,"IoTBits",-93,"08:bd:43:66:6a:86",6,-27,0) |
and after setting up a secure SSL connection, you can then feed that data to Google Geolocation API to get the location with a command that looks like (wifiAccessPoint data not filled here):
|
1 2 3 4 5 6 7 8 9 |
AT+CIPSEND=336 > POST /geolocation/v1/geolocate?key=AIzaSyCNStbdlDS_L HTTP/1.1 Host: www.googleapis.com Content-Type: application/json Content-Length: 166 {"homeMobileCountryCode": 310, "homeMobileNetworkCode": 410, "radioType": "gsm", "carrier": "Vodafone", "considerIp": "true", "cellTowers": [], "wifiAccessPoints":[]} |
Further research led me to m0xpd experimentation with Geolocation on ESP8266 last year, using both IP geolocation (found to be very inaccurate), and Google or Mozilla APIs, and posted his Arduino source code on Github. The Google API found his actual home in Manchester with just the information retrieved from the list of access points.
That also means that unsecured devices on the public Internet can easily be located, as an hacker logins to a router or IoT device, he just needs to run a command to find out the information required by his preferred geolocation API.

Jean-Luc started CNX Software in 2010 as a part-time endeavor, before quitting his job as a software engineering manager, and starting to write daily news, and reviews full time later in 2011.
Support CNX Software! Donate via cryptocurrencies, become a Patron on Patreon, or purchase goods on Amazon or Aliexpress





@tkaiser
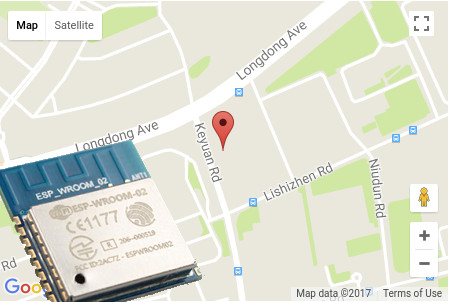
The map is the location of Espressif Systems office in Shanghai 🙂
Yes, it affects anything connected to the Internet with WiFi. That’s why I did not mention ESP8266 in particular in the last sentence. The many routers / modems directly connected to the Internet with default username / password are prime targets.
Thank you for the nice map screenshot (Longdong Avenue — LOL!) and especially the last sentence. But it should be noted that this is not related to ESP8266 at all since as soon as you ‘hacked’ any IoT device able to do wireless scans you’re already done. If you get access to a networked Raspberry Pi 3 for example all you need to locate the device is the output from ‘iwlist wlan0 scan’ (unless the Raspberry is in a rural area)
No need for this! The Internet of shitty things never receives upgrades, dnsmasq is almost everywhere and since yesterday we know how to open these boxes remotely 🙂
https://security.googleblog.com/2017/10/behind-masq-yet-more-dns-and-dhcp.html
Your last sentence is absolutely right and a bit scary!
Some time ago, I built a library for Arduino IDE that uses Google Geolocation to get position without GPS, listening to surrounding WiFi APs. It can be used with esp8266, esp32 and arduino mkr1000.
Code can be checked on https://github.com/gmag11/ESPWifiLocation
Regards
I didn’t know about the Google Geo service “Wifi-MAC => Location” … Thank you CNXsoft and Tkaiser.
@Sander Well, that such public services exist should be alarming since this is just the tip of the iceberg confirming the more serious problem that every wireless device out there that is trackable gets tracked and helps tracking everything around all the time (with data ending up somewhere in private data centers euphemistically called ‘the cloud’ so already accessible by 3 letter agencies and sooner or later by hackers or everyone since ‘cloud security’ is plain BS and has never worked so far). How are these databases fed? By dumb people combined with ‘smart phones’ with location services enabled and… Read more »
You can actually even track people with that. All you need is their IP address… If you can find somebody’s email, you can send him/her an email with some HTML code pointing to your server (for example an image), and get their IP once they open their email. They don’t even need to answer. Then you’d have to get into the system with that IP, which can be very easy or extremely hard depending on how well it is secured. But if you get inside, then you’d get that person location with some decent accuracy. Using VPN or the Tor… Read more »