There are serious security issues with the Internet of Things at all levels: hardware, software, network, and end-users. Microsoft Research NExT Operating Systems Technologies Group has been tasked with “exploring the goal of securing the vast number of low cost Internet connected devices coming online” with Project Sopris. They have shared their first technical report that identifies “seven properties of highly secure devices”, and describes their experiments towards designing microcontroller based prototype devices adapted from Mediatek MT7687 MIPS microcontroller, and exhibiting those seven properties.
The seven properties identifies by Microsoft team include:
- Hardware-based Root of Trust – Unforgeable cryptographic keys generated and protected by hardware. Physical countermeasures resist side-channel attacks.
- Small Trusted Computing Base – Private keys stored in a hardware-protected vault, inaccessible to software. Division of software into self-protecting layers.
- Defense in Depth – Multiple mitigations applied against each threat. Countermeasures mitigate the consequences of a successful attack on any one vector.
- Compartmentalization – Hardware-enforced barriers between software components prevent a breach in one from propagating to others.
- Certificate-based Authentication – Signed certificate, proven by unforgeable cryptographic key, proves the device identity and authenticity.
- Renewable Security – Renewal brings the device forward to a secure state and revokes compromised assets for known vulnerabilities or security breaches.
- Failure Reporting – A software failure, such as a buffer overrun induced by an attacker probing security, is reported to cloud-based failure analysis system.
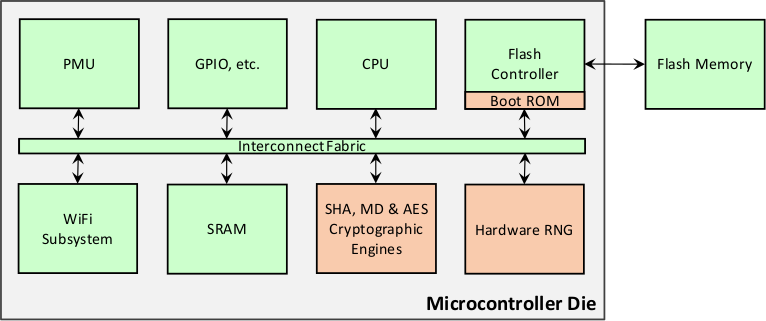
After noticing that most traditional MCUs lacks all of those 7 properties, they decided to modify Mediatek MT7687 whose block diagram is shown below…
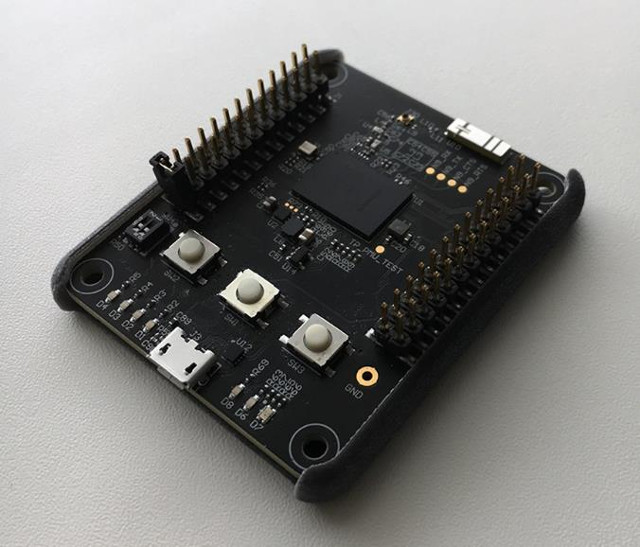
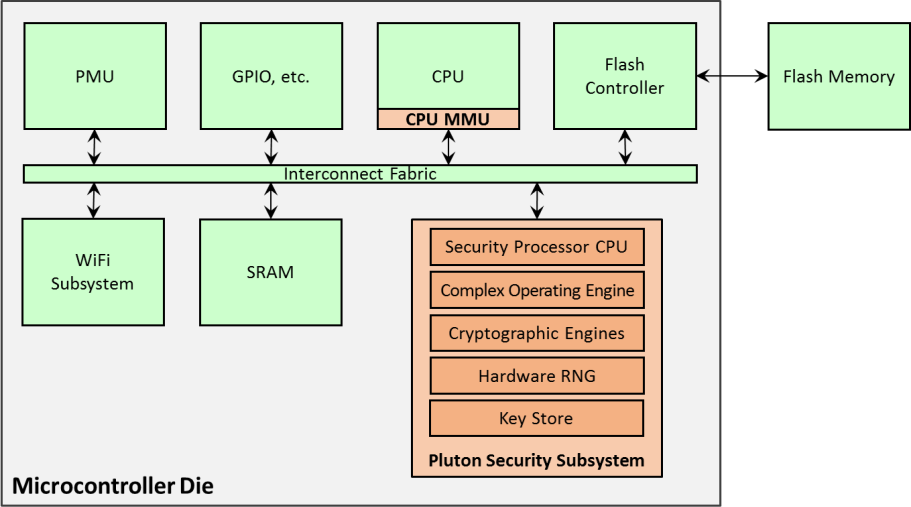
 … and replaced the crypto engines and hardware RNG with what Microsoft calls “Pluton security subsystem”, added a memory management unit (MMU) to the CPU, as well as more on-die SRAM. One this was done, they integrated in the prototype picture in the picture at the top of this post.
… and replaced the crypto engines and hardware RNG with what Microsoft calls “Pluton security subsystem”, added a memory management unit (MMU) to the CPU, as well as more on-die SRAM. One this was done, they integrated in the prototype picture in the picture at the top of this post.
So now we have a highly secure WiFi-enabled MCU. Since we are talking about security and WiFi, as a quick side node, it’s now possible to exploit Broadcom WiFi SoC security weaknesses to access the host operating systems in Android devices. This won’t affect Sopris MCU however.
Sopris development board is said to support the seven properties:
- Hardware-based root of trust – device secrets are protected in the Pluton security subsystem.
- Small trusted computing base – for most operations, the TCB for Sopris is isolated to the Pluton security subsystem.
- Defense in depth – between the upgraded CPU and the Pluton security system up to seven layers of defense are supported in Sopris.
- Compartmentalization – for example, separate compartments can be implemented using isolated address spaces enabled by the upgraded CPU.
- Certificate-based authentication – for example, private keys stored in the Pluton security subsystem can form the basis of a secure per-device certificate chain.
- Renewable security – for example, a software stack running on Sopris can use the multiple layers of hardware-protected defense in depth to implement renewable
security. - Failure reporting – for example, failure handling code that runs on the Sopris can collect data about failures and relay that information to a failure analysis service through Wi-Fi.
Going forward, Microsoft researchers plans to package Sopris into a simple device board design with software that can be shared with researchers and security experts across academia and industry.
Via EENews Europe

Jean-Luc started CNX Software in 2010 as a part-time endeavor, before quitting his job as a software engineering manager, and starting to write daily news, and reviews full time later in 2011.
Support CNX Software! Donate via cryptocurrencies, become a Patron on Patreon, or purchase goods on Amazon or Aliexpress. We also use affiliate links in articles to earn commissions if you make a purchase after clicking on those links.





Highly secured device runs high quality software, simple.
Microsoft and Mediatek do security together. I can only laugh so hard.
fscken trump mao cia privacy invaders and spies
I missed the part about “Project Sopris challenge” yesterday @ https://hackerone.com/project-sopris
They have cash prizes $2,500 to $15,000 for people who find security vulnerabilities.
@anon Trump-Kai-shek, surely? Mediatek is Taiwanese.
Looks like “privileged embedded processors with immutable proprietary software” is still a popular bad idea.