Kryptor FPGA, sometimes just called Kryptor, is a compact Intel/Altera MAX10 FPGA development board mostly designed for encryption, and acting as a dedicated Hardware Security Module (HSM) with a custom soft-core from Skudo OÜ. But obviously, you could also use the FPGA board for other purposes.
Hardware encryption can be quite more secure than software-based encryption with reduced attack surfaces, especially since data processing can be done in the FPGA RAM. The HSM can be used to encrypt files, videos, emails, IoT messages, etc… from various hardware platforms including Arduino and Raspberry Pi boards. Contrary to closed-sourced commercial solutions, the soft-core is open-source and as such can be verified by third parties to make sure there aren’t any backdoors or security flaws.
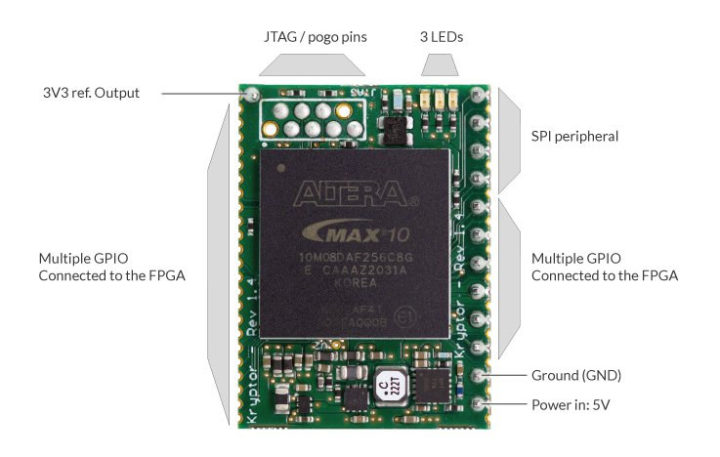
Kryptor FPGA specifications:
- FPGA – Intel/Altera MAX10 8K LE ( 10M08DAF256C8G) FPGA @ 100 MHz with 8000 logic elements (LE), 1376 Kb flash, 378 Kb total RAM, up to 250 GPIOs
- Host interface – SPI (preferred) up to 100 Kbps, I2C, or UART
- Security features
- Duplication protection – Anti-piracy duplication protection via chip ID (soft-cores are encrypted and cannot be executed on a different physical PCB)
- Encryption speed – Camellia symmetric encryption speed of up to 108 Mbps on a single core (but note the SPI link speed limit of 100 Kbps)
- Power Supply – 5V
- Power Consumption – 58 mAh (FPGA idle) to 64 mAh (FPGA encrypting)
- Dimensions – 31.2 x 22.8 mm
That’s it for the hardware. Implemented in Verilog, the HSM soft-core supports the following encryption features:
- Key-agreement scheme: Elliptic Curve Diffie-Hellman / Curve25519 (ECDH)
- Symmetric key block cipher: Camellia; up to four symmetric keys can be stored
- Asymmetric encryption: ECC25519; up to four asymmetric keys can be stored
- Cryptographic hash function: Skein
- True random number generator (TRNG): With ring oscillators as the source of entropy (FIGARO)
The company can also update the code to support additional functions such as Ed25519, AES256, SHA512, or Keccak, etc for legacy applications upon request.
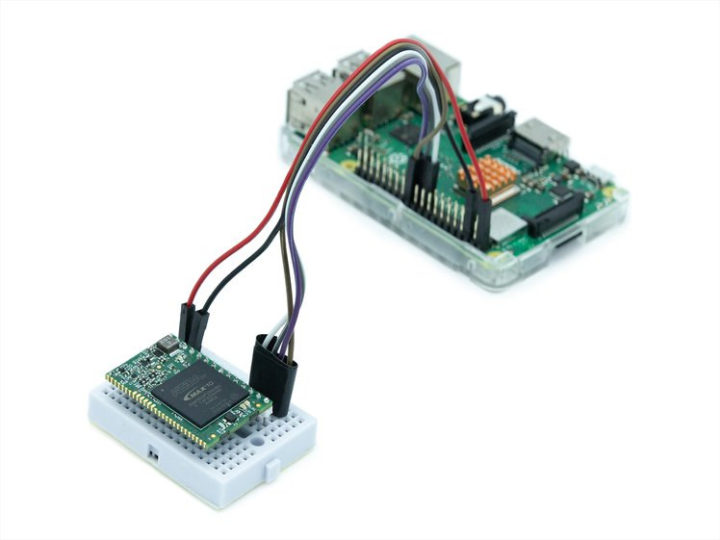
The company also provides a Raspberry Pi API library, a Linux Command Line Interface (CLI), and an Arduino library to control the board from a host connected over SPI, I2C, or UART.
I could not find a link to the tools, libraries, and soft-core yet, but the company will make those open-source, and you’ll eventually be able to download those from the company’s website. Note that since some/most governments have strict regulations with regards to importing and exporting devices with data encryption capabilities, the HSM soft-core will be pre-installed on the board.
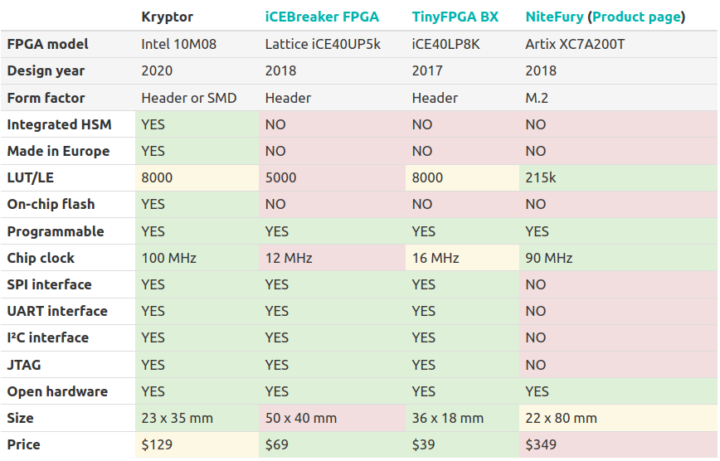
In the table above, SKUDO compares the Kryptor with other open-source hardware FPGA boards that were previously launched on Crowd Supply including iCEBreaker FPGA, TinyFPGA BX, and the NiteFury boards. None of those boards were specifically designed with encryption in mind, but the comparison still gives an idea of the differences between the boards.
You can get a SKUDO Kryptor FPGA board on Crowd Supply for a $129 reward that also includes a small breadboard and jumper wires. Shipping is free to the US, but adds $10 to the rest of the world, and the project should be completed by the end of February 2022. You may see an FPGA adapter in the list of rewards, but the company says it is not needed to flash the HSM soft-core.

Jean-Luc started CNX Software in 2010 as a part-time endeavor, before quitting his job as a software engineering manager, and starting to write daily news, and reviews full time later in 2011.
Support CNX Software! Donate via cryptocurrencies, become a Patron on Patreon, or purchase goods on Amazon or Aliexpress





Small correction: Contrary to what is stated in the table, NiteFury has JTAG
not bad
I wonder if it would be possible to backdoor it at RTL level?
“reduced attach surfaces“, should read, “reduced attack surfaces“, imho