CapibaraZero open-source firmware aims to offer a low-cost alternative to Flipper Zero for ESP32-S3-based hardware platforms and soon other gizmos with ESP32 wireless microcontrollers, notably the LilyGO T-Embed CC1101, similar to the original T-Embed with ESP32-S3 WiSoC, but also featuring a Texas Instruments CC1101 Sub-GHz microcontroller and an NXP PN532 NFC/RFID module. The Flipper Zero is a popular portable multi-tool for pentesters and hardware hackers based on STMicro STM32WB55 Bluetooth 5 LE & 802.15.4 wireless microcontroller and a TI CC1101 Sub-Ghz MCU that got involved in controversies such as a ban proposal in Canada last year due to its (dubious) potential use for car theft. Since then we’ve seen several alternatives such as Monstatek M1 (that’s yet to be delivered to backers…) and HackBat open-source hardware with Raspberry Pi RP2040, ESP8266 WiFi module, and the CC1101 RF transceiver. The CapibaraZero firmware offers another way to create your own cheap Flipper […]
Olimex USB-SERIAL-L is a USB-to-serial debug board with CTS/RTS pins, up to 3Mbps baud rate, adjustable voltage from 0.65V to 5.5V
There are already many USB-to-TLL debug boards on the market, but Olimex USB-SERIAL-L open-source hardware USB-to-serial board is more advanced than most with not only Tx/Rx pins, but also CTS/RTS pins, support for up to 3 Mbps speeds, and an adjustable voltage from 0.65V to 5.5V to cater to a wide range of boards. Olimex USB-SERIAL-L specifications: USB-to-serial chip – Silicon Labs CP2102N Seven signal lines – +5V, GND, CTS, RTS, TX, RX, Vref Baud rate from 50bps up to 3Mbps Output buffers with adjustable levels from 0.65 up to 5.5V USB – USB Type-C port for power and connect to host Misc – Power, Tx, and Rx status LEDs Power Supply Input – 5V via USB-C port Output – +5V to the target Dimensions – 35 x 35 x 8 mm (Custom 3D printed plastic box) Seven 200 mm long cables The Vref signal is used to adjust the […]
Waveshare RP2350-GEEK USB development board doubles as a debugger for Raspberry Pi and other Arm boards
Waveshare has recently launched the RP2350-GEEK USB development board which can also be used as a debugger for Raspberry Pi boards and other Arm-based targets. Built around the Raspberry Pi RP2350 MCU this development board/debugger features a 1.14-inch 65K color IPS LCD, a USB Type-A interface, a microSD card slot supporting SDIO and SPI communication, 16MB NOR-Flash, and multiple interfaces, including 3-pin SWD, USB to UART, and I2C ports. The board is compatible with standard CMSIS-DAP debugging tools like OpenOCD, which attaches to Raspberry Pi’s 3-pin debug connector for debugging. It also features open-source firmware for easy upgrades. Housed in a plastic case, the development board looks like a USB drive and is suitable for debugging, testing, and firmware development in IoT, embedded systems, and educational projects. Waveshare RP2350-GEEK Raspberry Pi debugger specifications Microcontroller – Raspberry Pi RP2350A MCU CPU – Dual-core Arm Cortex-M33 processor @ 150MHz Memory – 520KB internal RAM […]
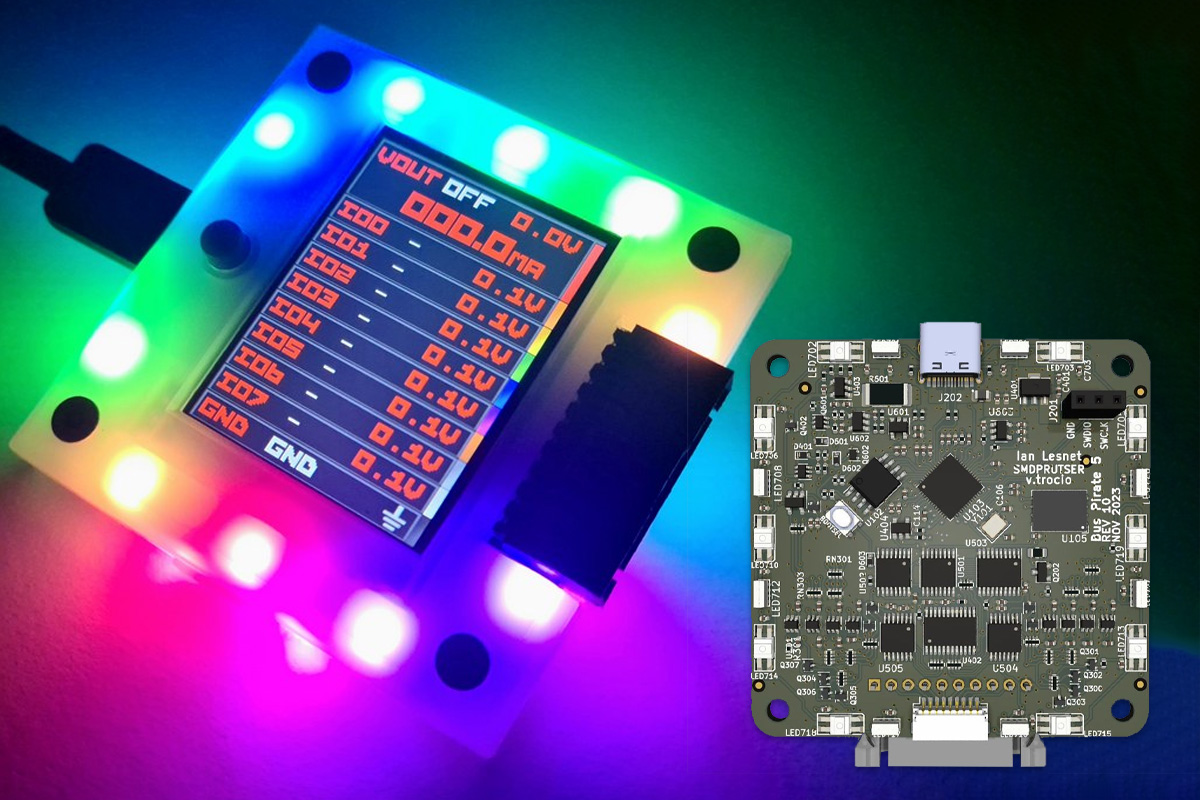
Bus Pirate 5XL and 6 hardware debugging tools utilize Raspberry Pi RP2350A and RP2350B microcontrollers
The Bus Pirate 5XL and 6 are open-source hardware debugging tools respectively based on Raspberry Pi RP2350A and RP2350B and designed to simplify interaction with various bus protocols like 1-Wire, I2C, SPI, UART, several LEDs, and more. The idea is to send commands to a chip or sensor and get the response, without writing a single line of code making it ideal for hardware hacking and tinkering. The devices feature buffered I/O pins with voltage and current measurement, a programmable power supply with current limiting, an RGB LCD for pin status and info, and an auxiliary header for connecting logic analyzers. All these features make this device useful for applications like debugging circuits, prototyping projects, and reverse engineering devices. The new devices are updates to the Bus Pirate 5 based on Raspberry Pi RP2040 MCU. You’ll find Bus Pirate specifications for the three models in the table below. The original […]
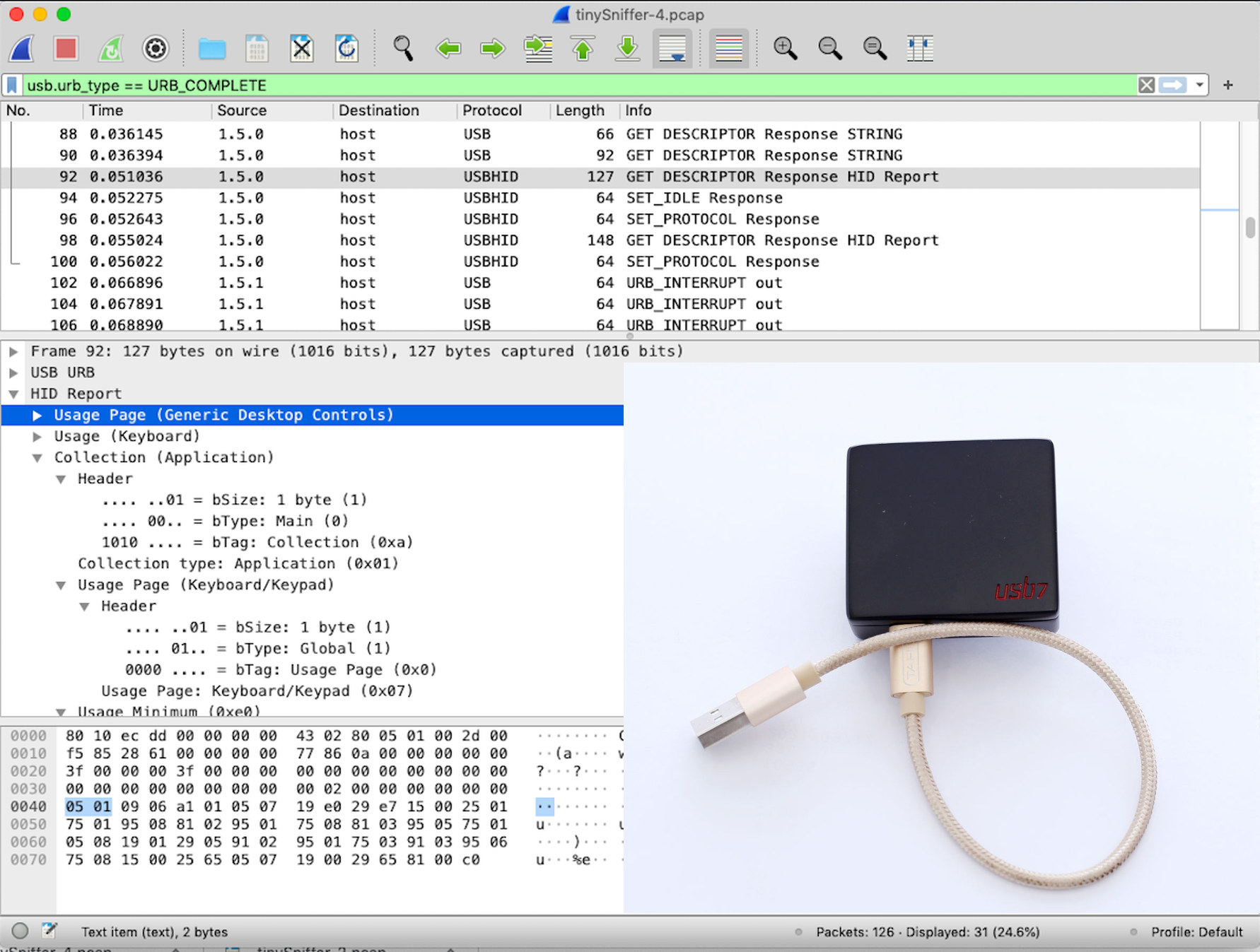
tinySniffer WiFi-connected USB sniffer is based on NanoPi NEO Air SBC
TinySniffer is a USB sniffer based on the Allwinner H3-powered NanoPi Neo Air SBC, designed to capture USB 1.x and 2.0 packets remotely, and whose captured data is compatible with the popular Wireshark packet analyzer tool. Wireshark can already be used to capture USB packets on its own and I reverse-engineered a USB capture video solution that way in the past, but this method has some limitations, for instance, it does not capture some low-level USB packets, in which case a hardware USB sniffer like Total Phase Beagle USB, the PhyWhisperer USB, or the tinySniffer is required. The micro USB OTG port of the NanoPi NEO Air SBC is connected to the host computer and the company added a USB 2.0 Type-A port connected to the USB interface on the GPIO header to connect a device under test such as a USB keyboard, a USB Ethernet dongle, a USB printer, […]
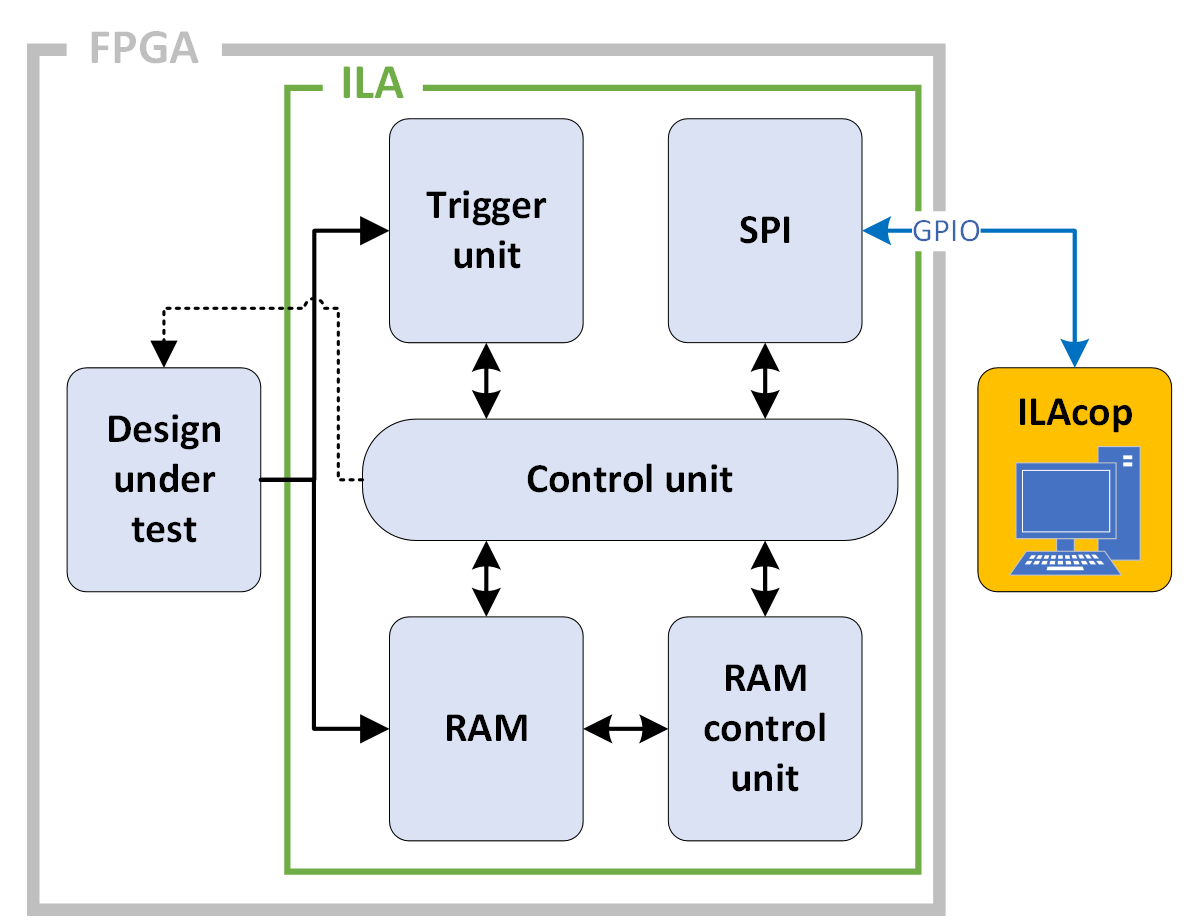
GateMate Integrated Logic Analyzer (ILA) deep dive
CNXSoft: This is a guest article by Dave Fohrn, Embedded Software Engineer at Cologne Chip AG, that goes into detail about the company’s open-source integrated logic analyzer (ILA) for GateMate FPGA chips. A field-programmable gate array (FPGA) is a highly flexible integrated circuit in which complex logic circuits can be configured. They are often used as custom computing units in digital circuits because of their ability to process data quickly and in parallel using individually configured circuits. The digital circuits designed specifically for FPGAs are usually developed in a hardware description language such as Verilog or VHDL and are known as gateware. The term “gate” refers to the configurable digital logic units in the FPGA on which the individual gate circuits are implemented. An effective design can accelerate the computing process by strategically utilizing the various resources available in the FPGA, processing data in parallel, and intelligent implementing pipelining. A […]
SBC software news – Armbian 24.5.1, DietPi 9.4, and Otii server for the Raspberry Pi 4/5
There’s been some notable software news for single board computers (SBCs) in the last few weeks with the release of Armbian 24.5.1 Havier with a focus on stability and UX improvement, the release of DietPi 9.4 lightweight Debian distritions for SBCs, and Otii server, the software for Qoitech Arc power supply, meter, and DAQ, has been finally released for the Raspberry Pi 4/5. Armbian 24.5.1 Havier Armbian announced 24.5.1 Havier on May 25 with bug fixes and improvements as a point release, but also some new boards. Here are some of the highlights. New boards Orange Pi 5 Pro FriendlyElec CM3588 NAS board Radxa ROCK 5 ITX Radxa Zero 3E/3W Avaota A1 SBC SK-AM68 board tqma8mpxl board CSC Hinlink H6xk boards RK3588-based Cool Pi CM5 EVB Improve Khadas support Resolve Rockchip patch maintenance nightmare Add functionality to freeze git resources Improve support for Radxa Rock S 0 and test USB […]
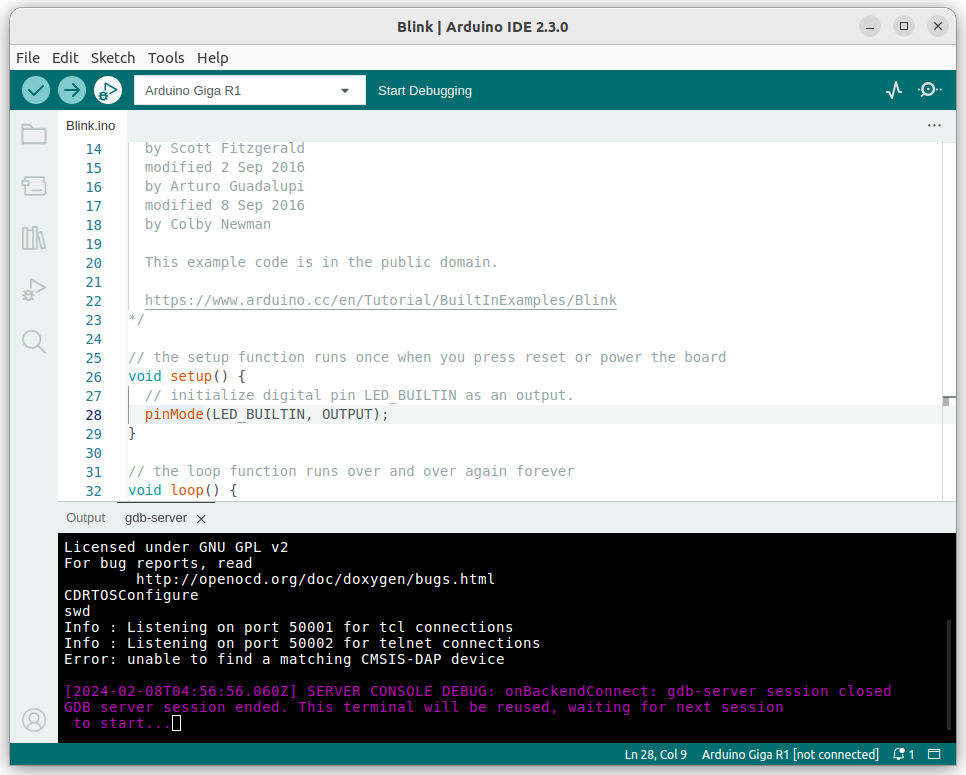
Arduino IDE 2.3 released with the Debug feature now considered stable
Arduino IDE 2.3 has just been released with a range of bug fixes and improvements, but the main change is that the debug feature is not experimental anymore and is now considered stable. Bug fixes include addressing CVE-2023-4863 security flaw (See GitHub for related commits) and based on the wording used in the announcement it looks to be the only one… So the main news is that the Debug feature is now fully incorporated into the IDE. But what is it exactly? The new documentation website explains that Arduino CLI 0.9.0 and Arduino IDE 2.x support “sketch debugging” with openocd server. Arduino also explains it’s currently supported by Arduino boards based on the Mbed core including GIGA R1 WiFi, Portenta H7, Opta, Nano BLE, and Nano RP2040 Connect, and Renesas-based boards such as UNO R4 and Portenta C33 will get support very soon. The company also says they are working […]