Most Arm processors and Armv8-M microcontrollers support Arm TrustZone security with hardware-enforced isolation built into the CPU. But so far, I had not read anything about equivalent solutions for RISC-V processors.
It turns out Hex-Five’s MultiZone security is one of the RISC-V hardware-security providing an answer to Arm TrustZone, and besides checking out the presentation slides, you can also watch the video filmed at RISC-V Workshop Taiwan last March. But what brought me to write about RISC-V security is SiFive announcement for their Shield open security platform for RISC-V processors
SiFive Shield Overview
SiFive Shield is an open, scalable security platform designed for RISC-V processors. It supports root-of-trust, customizations, and offers per-memory protected memory regions and multi-core privilege modes. Combined with SiFive WorldGuard, SiFive Shield enables greater isolation.
SiFive WorldGuard Isolation
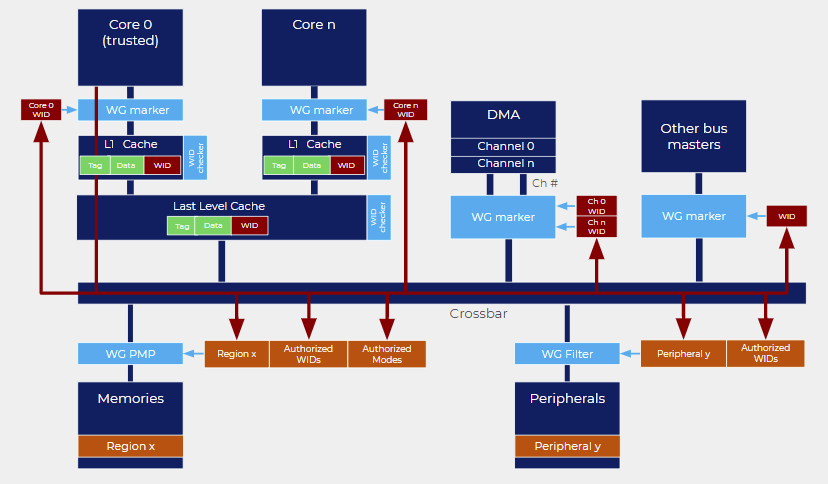
SiFive WorldGuard is a fine-grain security model for isolated code execution and data protection. It offers core-driven and process-id driven modes to offer data protection for core, cache, interconnect, peripheral, and memory.
The chart above illustrates how World ID markers are used to isolate processes from each other in multi-core processors. For single-core processors, such as the ones found in some embedded systems, PID-driven world ID’s can be used to isolate execution between user and machine mode.
Root of Trust
SiFive’s root of trust is based on open specifications and an open-source software platform. SiFive Shield further enables secure storage of keys on-chip with unique IDs which enables key and certificate provisioning at the factory.
Threat Prevention via Memory Protection
The security platform leverages Physical Memory Protection (PMP) and Physical Memory Attributes (PMA) part of RISC-V ISA in order to set limitations and privileges on memory ranges and/or memory-mapped peripherals.
Crypto-Engines
The SiFive Shield architecture also includes crypto hardware such as a true random number generator (TRNG), an AES cryptographic engine, a secure hash crypto-engine with support for SHA-2 and SHA-3 standards, and RSA and ECDSA public-key cryptography is also supported. The crypto-engines are said to be protected against SPA/DPA/EMA attacks.
Software
SiFive Shield is supported by a software platform based on open-source software that includes FreeRTOS and Linux OS operating systems, SiFive Freedom Metal and Freedom SDK toolchains.
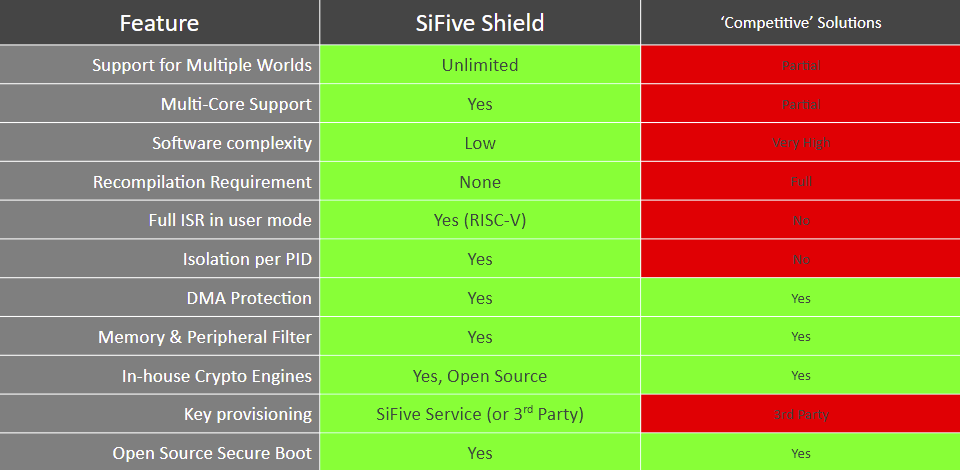
SiFive Shield vs “Competitive Solutions”
The company also provided a comparison between Shield and other solutions, but it’s not clear whether this refers to Arm TrustZone or other RISC-V security solutions.
You may find additional details in the press release.

Jean-Luc started CNX Software in 2010 as a part-time endeavor, before quitting his job as a software engineering manager, and starting to write daily news, and reviews full time later in 2011.
Support CNX Software! Donate via cryptocurrencies, become a Patron on Patreon, or purchase goods on Amazon or Aliexpress. We also use affiliate links in articles to earn commissions if you make a purchase after clicking on those links.




MultiZone looks genuinely interesting. Would be nice to see an ESP32-like chip with a RISC-V and their multizone iot stack as the basis of the SDK.
Thought this might interest some but not which cnx post suits it best.
“”Trace and debug claim for RISC-V IP challenged by UltraSoC
SiFive has announced hardware trace and debug for RISC-V processor IP. Called SiFive Insight, it is “industry’s first combined trace and debug solution for the freely-available, open-specification RISC-V ISA”, said SiFive. it is intended to “meet customer demand and expectations for the capability to access, observe, and control products deploying SiFive’s RISC-V Core IP portfolio”.
UltraSoC CEO Rupert Baines expressed surprise at the claim: “I’m amused to see SiFive claim ‘industry’s first trace and debug solution for RISC-V ISA’. There was I thinking that UltraSoC had been shipping trace & debug for RISC-V for at least two years, silicon proven in multiple customers, including many SiFive customers,” said Baines, “but what do I know?” ”
electronicsweekly
Unfortunately Multizone doesn’t do what it says it does. Just look closely at the repo if you don’t believe me.