Tails (The Amnesic Incognito Live System) is a Linux distribution that allows you to use the Internet anonymously and circumvent censorship via the Tor network. It leaves no trace, and is said to use “state-of-the-art” cryptographic tools to encrypt files, emails and instant messages. It’s distributed as a live image that boots from a DVD drive, a USB stick, or an SD card. Tails v1.0 has recently been released. so let’s give it a quick try. Tails is currently only available for x86 (32-bit), no ARM image yet. The source code is available via a git repo.
Let’s download the ISO image (mirror), and signature. Alternatively you can download both via BitTorrent.
To make sure the image is not compromised it’s recommend to verify the integrity of the ISO image with the signature we’ve just downloaded. You’ll also need a signing key The are several methods, but I’ve opened a terminal, and run the following two commands in the directory where the ISO, signature and signing key files are located:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 |
~/tails$ gpg --keyid-format long --import tails-signing.key gpg: key 1202821CBE2CD9C1: public key "Tails developers (signing key) <tails@boum.org>" imported gpg: Total number processed: 1 gpg: imported: 1 (RSA: 1) gpg: no ultimately trusted keys found ~/tails$ gpg --keyid-format long --verify tails-i386-1.0.iso.sig tails-i386-1.0.iso gpg: Signature made Monday, April 28, 2014 AM03:02:35 ICT gpg: using RSA key 1202821CBE2CD9C1 gpg: Good signature from "Tails developers (signing key) <tails@boum.org>" gpg: aka "T(A)ILS developers (signing key) <amnesia@boum.org>" gpg: WARNING: This key is not certified with a trusted signature! gpg: There is no indication that the signature belongs to the owner. Primary key fingerprint: 0D24 B36A A9A2 A651 7878 7645 1202 821C BE2C D9C1 |
So that’s all good as it returns a Good Signature. The WARNING simply means I haven’t signed the key myself, but the ISO image should not be compromised. In case of error, you should see a line with:
|
1 |
gpg: BAD signature from "Tails developers (signing key) <tails@boum.org>" |
Now you should burn the ISO to a DVD disk or USB flash drive / SD card, and insert it to the machine your want to use. If it does not boot, you’ll have to check your BIOS settings to enabled DVD or USB boot. For convenience, I have booted Tails Live ISO image from VirtualBox, but this is not recommended as the host machine will store data, and can be used to monitor your activity.
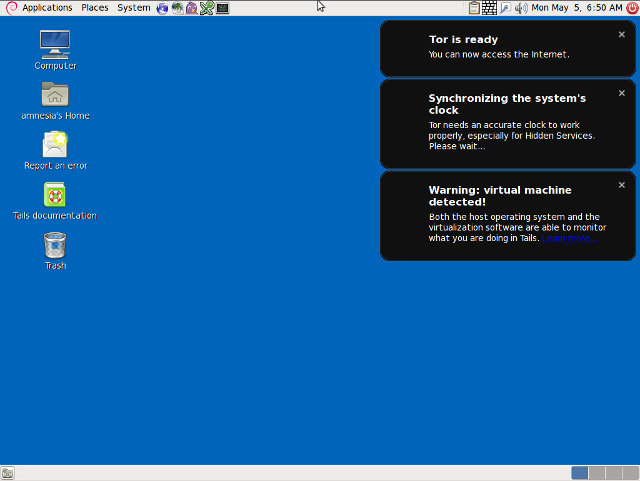
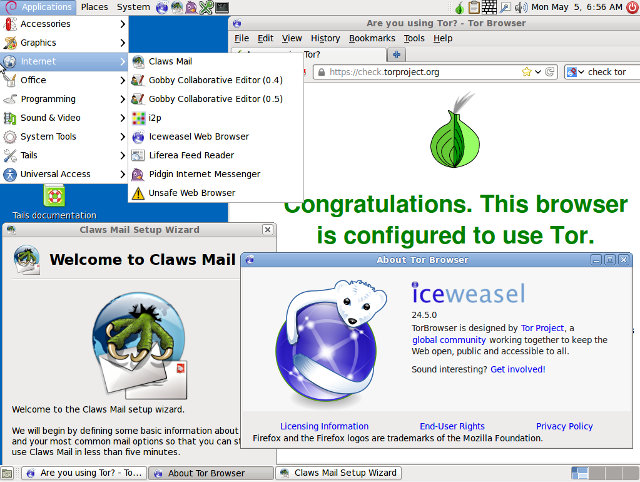
For the very first boot, you’ll be asked if you need more options and/or want to login. There’s no password, because nothing will be stored. You’ll see the Debian based desktop above with some notifications about time synchronization for Tor, and in my case, an extra warning because I’m using a virtual machine. The web browser is Tor Browser / IceWeasel and as you can see from the first screenshot in this post, it’s indeed using the Tor network which randomizes and anonymizes your IP address. As you browse the web, you’ll find out most ads won’t be displayed to prevent user’s tracking, and traffic default to HTTPS when available. There’s also an “Unsafe Browser” that should only be used in special cases.The mail client is Claws Mail which I haven’t tried but is supposed to provide GPG encryption. Encrypted message is made possible via Pidgin with Off-the-record (OTR) encryption. Beside Internet applications should also have program such as Gimp, Audacity and LibreOffice pre-installed in the image.
Since it’s a live image by default, you can’t save anything. If you’re booting from a DVD it will stay that way, but if you’re using Tails from a USB flash drive or SD card, there’s a tool to create a Persistent (Encrypted) Partition to save files.
Please be aware that Tails is only a tool, and you should educate yourself by reading the documentation. For example, you should not login to your bank account with Tails, as obviously our bank has your contact details. If you open an email account or register to any other website on Tails, and then later access this email or/and website via another non-protected operating systems, you can be traced, and so on… You’ll probably want a standard OS for day to day tasks, and only use Tails if you really need to remain anonymous.

Jean-Luc started CNX Software in 2010 as a part-time endeavor, before quitting his job as a software engineering manager, and starting to write daily news, and reviews full time later in 2011.
Support CNX Software! Donate via cryptocurrencies, become a Patron on Patreon, or purchase goods on Amazon or Aliexpress





Since it’s a live image by default you can save anything.
I would think that the MOST IMPORTANT WORD in this sentence is actually wrong.
@j0539h
Oops. “NOT” somehow went missing…